Posts
5610Following
351Followers
551Jarkko Sakkinen
jarkko
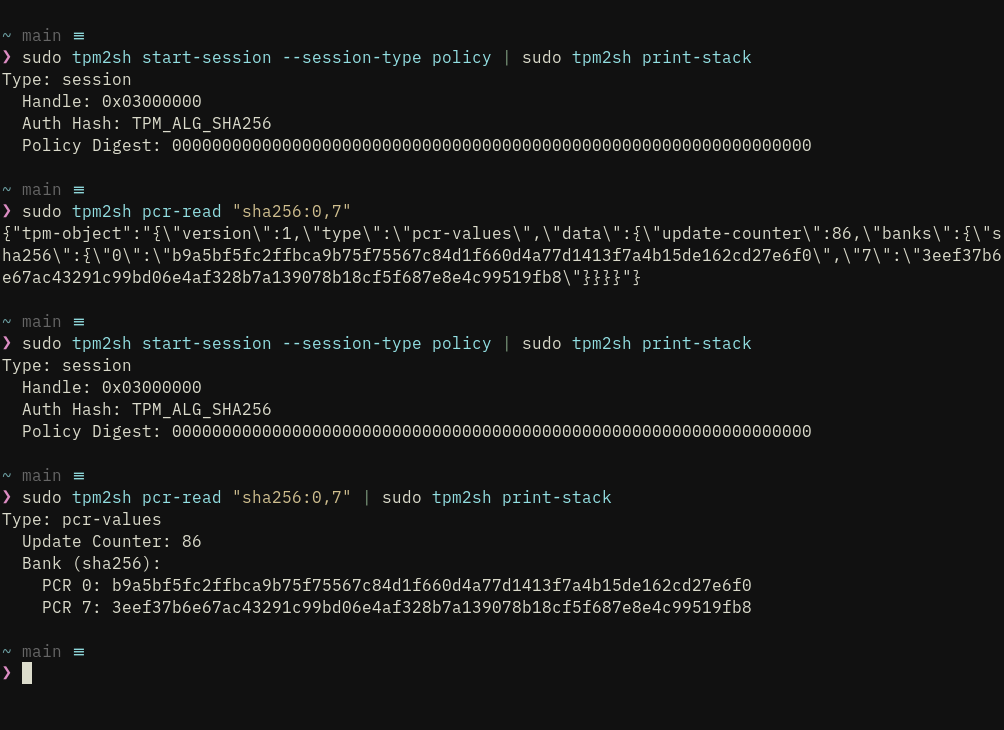
i.e. pcr-read by default does not by default print anything readable. it reads pcrs from tpm and produces the blob to the stack basically. so this prin-stack changes all commands output human-readable
Jarkko Sakkinen
jarkko
still a bit unstable feature as i'm also refactoring the stack itself sleeker but getting there
Jarkko Sakkinen
jarkko
Edited 9 months ago
I actually would have to test run it which I might do. It does have fixed-limited loops which I would imagine eBPF compiler to be able to unroll but other than that I'm not sure if there are backward jumps in tpm2_protocol. I'll try this some day :-)
Obviously it will fail when if I deploy it to filter but it is still interesting to see how and where.
Obviously it will fail when if I deploy it to filter but it is still interesting to see how and where.
Jarkko Sakkinen
jarkko
The whole project has been about doing placeholder solution and then rewriting it. I even "rewrote" tpm2_protocol twice, first I thought it was fine when I got it working on static objects. Then I realized that I need to do things from ground up again tweaking the implementation from every possible location to make it robust enough with lifetimes to be able to use TpmObject as dyn trait.
But yeah, this is something I knew that would happen when aiming for product quality first time in Rust :-) It was a time investment really. I learned so much from this that I cannot really even begin to describe it ...
But yeah, this is something I knew that would happen when aiming for product quality first time in Rust :-) It was a time investment really. I learned so much from this that I cannot really even begin to describe it ...
Jarkko Sakkinen
jarkko
@Aissen yeah true :-) i'm actually looking forward to get rid of json. i already gave on json structure for pcrs as i can parse tpmlpcrselection on fly (or that is like the whole point of this project)
i.e. from json stack a migration is ongoing towards TPM object stack...
i.e. from json stack a migration is ongoing towards TPM object stack...
Jarkko Sakkinen
jarkko
@Aissen ah OK. for protocol i have standalone test program that outputs kselftest exit codes. For that subcrate I keep even dev-dependencies absolute zero.
tpm2sh is playground for testing that care but still i try to decrease its size when i find something where i can slim it down :-)
tpm2sh is playground for testing that care but still i try to decrease its size when i find something where i can slim it down :-)
Jarkko Sakkinen
jarkko
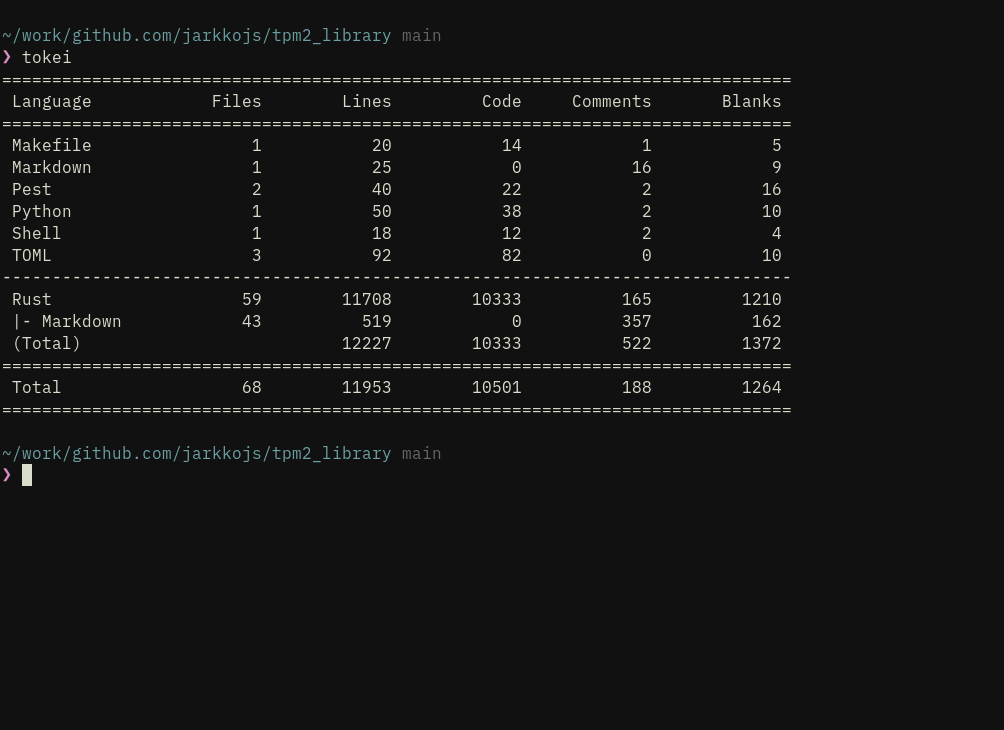
I'm quite optimistic that SLOC will be reduced as few months pass as this was put together in a very short period of time :-) i processed the architecture for a year tho in my head so that's why it came together so fast.
Jarkko Sakkinen
jarkko
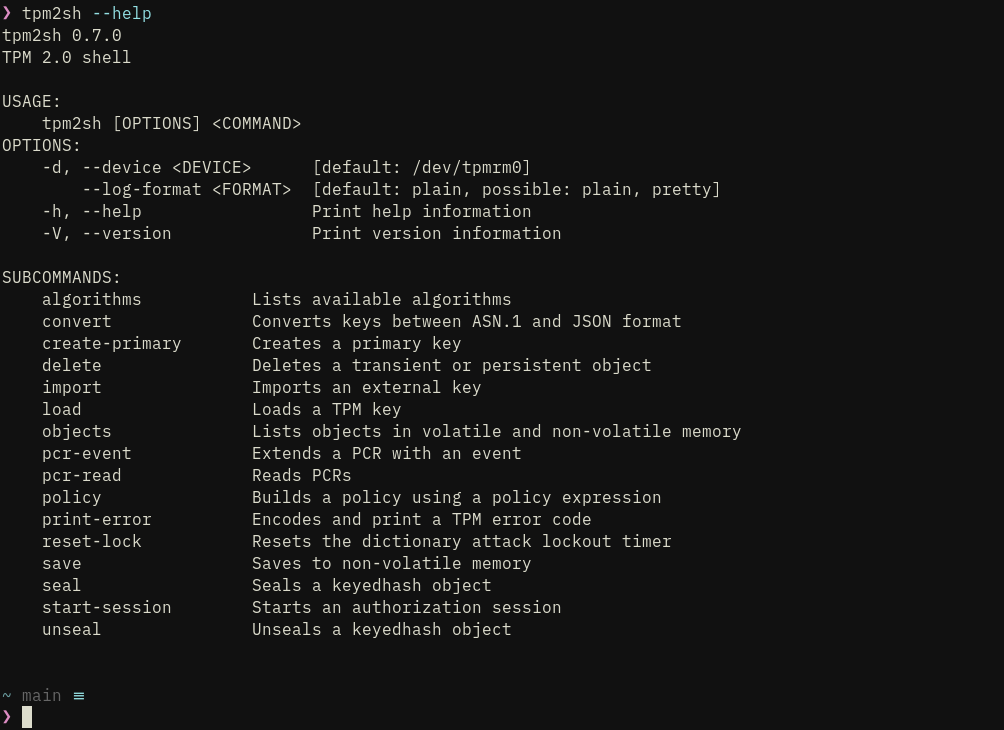
tpm2sh starts to look pretty good and has at least the features i want it to have for kernel testing.
tpm2_protocol is "kernel-ready" (including Box<dyn TpmObject>, which is essential for a driver uapi) and this the full list of commands it lacks for 100% TCG TPM 2.0 specification coverage:
https://github.com/puavo-org/tpm2_library/issues/4
I'm pretty much done with this project for the moment :-)
tpm2_protocol is "kernel-ready" (including Box<dyn TpmObject>, which is essential for a driver uapi) and this the full list of commands it lacks for 100% TCG TPM 2.0 specification coverage:
https://github.com/puavo-org/tpm2_library/issues/4
I'm pretty much done with this project for the moment :-)
Jarkko Sakkinen
jarkko
@Aissen sorry, what does "syn-free" mean? :-)
I just tagged 0.7.0 version you can check up yourself: https://github.com/puavo-org/tpm2_library
crypto crates add up a bit for tpm2sh but i want consolidate enough of that so that i can use this for e.g. kernel testing w/o having to use openssl too much
when i started to make tpm2sh it was this cover letter that i used as my source for minimal set of features that i need :-)
https://lore.kernel.org/linux-integrity/20240528210823.28798-1-jarkko@kernel.org/
I just tagged 0.7.0 version you can check up yourself: https://github.com/puavo-org/tpm2_library
crypto crates add up a bit for tpm2sh but i want consolidate enough of that so that i can use this for e.g. kernel testing w/o having to use openssl too much
when i started to make tpm2sh it was this cover letter that i used as my source for minimal set of features that i need :-)
https://lore.kernel.org/linux-integrity/20240528210823.28798-1-jarkko@kernel.org/
Jarkko Sakkinen
jarkko
@devcoffee there's no need to access tpm i'd just like to know if i can run the parser inside eBPF
Jarkko Sakkinen
jarkko
A spec update for a single new commands takes about 15 minutes to implement. I just di d that for ZGen2Phase:
tpm_struct! {
#[derive(Debug, PartialEq, Eq, Clone)]
TpmZGen2PhaseCommand,
TpmCc::ZGen2Phase,
false,
true,
1,
{
pub in_qsb: Tpm2bEccPoint,
pub in_qeb: Tpm2bEccPoint,
pub in_scheme: TpmiEccKeyExchange,
pub counter: u16,
}
}
tpm_response! {
#[derive(Debug, PartialEq, Eq, Clone)]
TpmZGen2PhaseResponse,
TpmCc::ZGen2Phase,
false,
true,
{
pub out_z1: Tpm2bEccPoint,
pub out_z2: Tpm2bEccPoint,
}
}
In addition a single line is required to ordered by cc dispatch list (there is compilation check for order):
(TpmZGen2PhaseCommand, TpmZGen2PhaseResponse, ZGen2Phase),
tpm_struct! {
#[derive(Debug, PartialEq, Eq, Clone)]
TpmZGen2PhaseCommand,
TpmCc::ZGen2Phase,
false,
true,
1,
{
pub in_qsb: Tpm2bEccPoint,
pub in_qeb: Tpm2bEccPoint,
pub in_scheme: TpmiEccKeyExchange,
pub counter: u16,
}
}
tpm_response! {
#[derive(Debug, PartialEq, Eq, Clone)]
TpmZGen2PhaseResponse,
TpmCc::ZGen2Phase,
false,
true,
{
pub out_z1: Tpm2bEccPoint,
pub out_z2: Tpm2bEccPoint,
}
}
In addition a single line is required to ordered by cc dispatch list (there is compilation check for order):
(TpmZGen2PhaseCommand, TpmZGen2PhaseResponse, ZGen2Phase),
Jarkko Sakkinen
jarkko
Edited 9 months ago
It's a lot to say but I rarely cause over or underflows C. Cannot even remember when was the last time. But this structural integrity area is where I get more precision when using Rust.
I.e. I can almost formally do a yes/no check whether some sequence on-wire (given Box<dyn TpmCommand> capability) of data is command or response or something that differs only per byte of the set of legit commands or responses. That nails the key difference.
I.e. I can almost formally do a yes/no check whether some sequence on-wire (given Box<dyn TpmCommand> capability) of data is command or response or something that differs only per byte of the set of legit commands or responses. That nails the key difference.
Jarkko Sakkinen
jarkko
IMHO the thing in Rust and drivers is not memory safe per se or like "overflow check type of stuff".
It's the structural integrity check that levels up over C really. E.g. in C world I check that a TPM command holding buffer is not too large.
In Rust world I'll check in byte granularity that the data coming from user space and the chip is correct.
It's the structural integrity check that levels up over C really. E.g. in C world I check that a TPM command holding buffer is not too large.
In Rust world I'll check in byte granularity that the data coming from user space and the chip is correct.
Jarkko Sakkinen
jarkko
Edited 9 months ago
Do rustc eBPF branches unroll loops if they have const limit known by compiler?
I'm just thinking of theory of running tpm2_protocol inside eBPF filter i.e., is it possible and how much effort it would take it realize.
would be just a cool demo
it has lot of characteristics i.e. no-alloc (fully in-stack) and test program compiles without cargo with just rustc.
#linux #kernel #ebpf #rust #tpm
I'm just thinking of theory of running tpm2_protocol inside eBPF filter i.e., is it possible and how much effort it would take it realize.
would be just a cool demo
it has lot of characteristics i.e. no-alloc (fully in-stack) and test program compiles without cargo with just rustc.
#linux #kernel #ebpf #rust #tpm
Jarkko Sakkinen
jarkko
@Aissen i also migrated to json from serde_json for the sake of simplicity and clarity (for me that mainly simplicy and clarity of the binary). i'm constantly trying to find dependencies from tpm2sh that do less rather than more and have less recursive dependencies :-)
thinking more of the binary also improves productivity in long-term investment as linking times go much lower, which is like the main bottleneck when compiling rust. you can easily get a high-end ryzen workstation melt on that process if you are sloppy with deps :D (i've got my 9950X workstation OOM because of that on some projects).
thinking more of the binary also improves productivity in long-term investment as linking times go much lower, which is like the main bottleneck when compiling rust. you can easily get a high-end ryzen workstation melt on that process if you are sloppy with deps :D (i've got my 9950X workstation OOM because of that on some projects).