Posts
5454Following
347Followers
543Jarkko Sakkinen
jarkko
@lanodan It's like with Rust ecosystem that they've made the right analysis of situation i.e. for most stuff we put everything to somekind of container etc. and for 99% of stuff we pile it's great call.
But the thing is nothing ever works ideally except maybe computer science class and there is 1% where that makes absolutely no sense. So to level up I'd address these type of details too, and accept the reality. Up until that Rust is pretty much destined to be a Java for system programming sandboxed by C based ecosystem.
But the thing is nothing ever works ideally except maybe computer science class and there is 1% where that makes absolutely no sense. So to level up I'd address these type of details too, and accept the reality. Up until that Rust is pretty much destined to be a Java for system programming sandboxed by C based ecosystem.
Jarkko Sakkinen
jarkko
@lanodan it's a special corner case and i'm talking about deployments at scale of even hundreds or thousands nodes and fucking armed guards and shit xD usually corps have this thing called Secure Development Lifecycle (SDL) process that everything to needs to comply and it is hard to map to bunch of Rust programs with random versions of random crypto.
Jarkko Sakkinen
jarkko
@lanodan it does not rely on assumptions. it is more like that in production you often need to have somehow certified/audited crypto. I.e. it is irrelevant how strong or weak the crypto is in some sense as long as it has gone through that process.
thus, statically linked crypto is a problem.
also it is a problem even when the crypto would audited that you can only hotfix all deployed rust by updating all possible rust programs. it's much easier to hotfix a single crypto entity, which could be DSO.
thus, statically linked crypto is a problem.
also it is a problem even when the crypto would audited that you can only hotfix all deployed rust by updating all possible rust programs. it's much easier to hotfix a single crypto entity, which could be DSO.
Jarkko Sakkinen
jarkko
Easiest way to test Windows compilation in Linux for Rust crate?
I'd like to add a target for https://git.kernel.org/pub/scm/linux/kernel/git/jarkko/tpm2-protocol.git
I'd like to add a target for https://git.kernel.org/pub/scm/linux/kernel/git/jarkko/tpm2-protocol.git
Jarkko Sakkinen
jarkko
It would be comptetitive advantage for Rust to have first class DSO support. It's like 99% of things Rusts static linking model is exactly right thing to do but for 1% of use cases you should just have a DSO.
Prime examples:
- Core crypto libraries. These need to be hotfixe when CVE arises.
- Core graphic libraries.
- System GUI libraries.
Prime examples:
- Core crypto libraries. These need to be hotfixe when CVE arises.
- Core graphic libraries.
- System GUI libraries.
Jarkko Sakkinen
jarkko
i feel like a winner now when I reached TPM_RC_INTEGRITY. this is easy to squash :D crypto works fully or does not work at all
Jarkko Sakkinen
jarkko
day 2 fighting with TPM2_Import. and it's not the first time. the protocol crate is doing nothing wrong, it's a bug in tpm2sh
Jarkko Sakkinen
jarkko
I should have remember by now that for KDFa's you feed "DUPLICATE\0" not "DUPLICATE" and so forth. But no, I fought with TPM_RC_VALUE for half a day.
Jarkko Sakkinen
jarkko
Edited 8 months ago
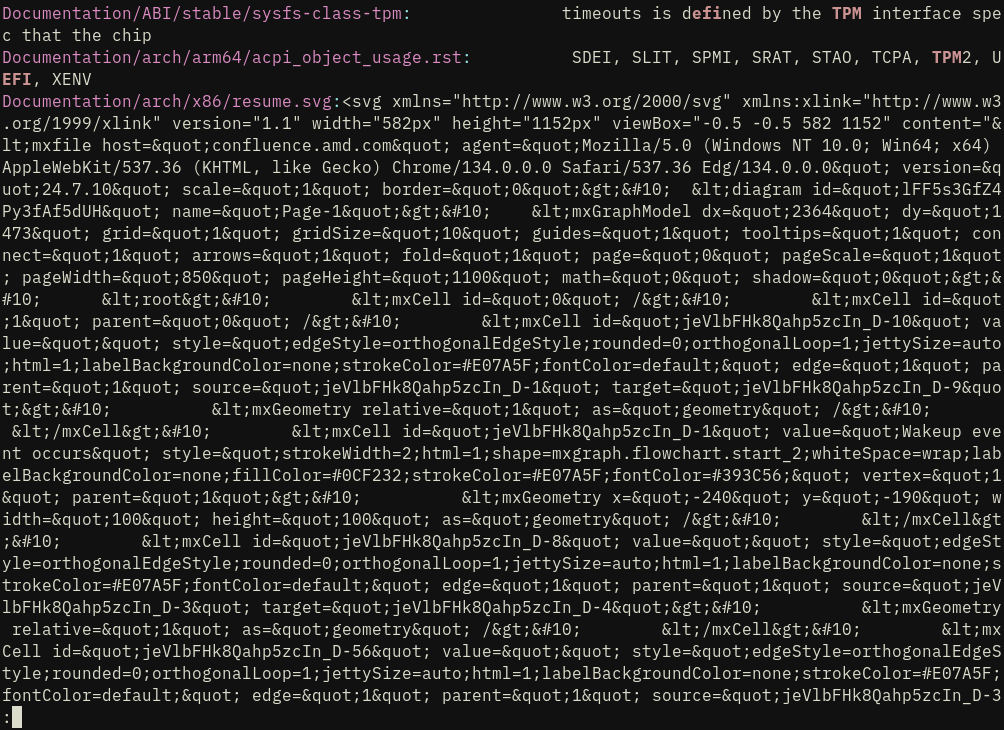
this SVG garbage fuck. is there something we could put .gitattributes, .gitignore or something that would make it not to destroy git grep experience?
Jarkko Sakkinen
jarkko
Edited 8 months ago
Now it is carved to the stone:
https://github.com/puavo-org/tpm2sh/commit/f95d6aae1f5212c39349a77e066b4ceeb2ef580c
I'll need this once I have bandwidth to refine:
https://lore.kernel.org/linux-integrity/20240528210823.28798-1-jarkko@kernel.org/
https://github.com/puavo-org/tpm2sh/commit/f95d6aae1f5212c39349a77e066b4ceeb2ef580c
I'll need this once I have bandwidth to refine:
https://lore.kernel.org/linux-integrity/20240528210823.28798-1-jarkko@kernel.org/
Jarkko Sakkinen
jarkko
Edited 8 months ago
In the sense confidential computing holds it promise that since the hardware is inaccessible by practical means to *everyone*, you need to execute that type of code in your head. It is as confidential at least as computing can ever get [Side-note: even the name of the field is incorrect terminology at least when reflecting on how the terminology is usually defined in the field of information security. The so called "CIA Triad" defines trust as the sum of availability, confidentiality and integrity.]
This is what I literally do with SGX patches:
1. I pick up Intel SDM (which is IMHO pretty good ISA reference overall, zero complains on that).
2. I read the pseudocode for new opcodes or revisit old ones.
3. I look it is applied in kernel patch
4. Finally I "hallucinate" its execution :-----)
And based on this mental execution procedure I ack/nak patches.
You can extrapolate from this that probably most of any type of CoC code in kernel are the least audited areas of the Linux kernel source code. Even if working for a CPU company, it is hard to really hammer the code, if your only access to the hardware is a shitty company cloud.
This is what I literally do with SGX patches:
1. I pick up Intel SDM (which is IMHO pretty good ISA reference overall, zero complains on that).
2. I read the pseudocode for new opcodes or revisit old ones.
3. I look it is applied in kernel patch
4. Finally I "hallucinate" its execution :-----)
And based on this mental execution procedure I ack/nak patches.
You can extrapolate from this that probably most of any type of CoC code in kernel are the least audited areas of the Linux kernel source code. Even if working for a CPU company, it is hard to really hammer the code, if your only access to the hardware is a shitty company cloud.
Jarkko Sakkinen
 repeated
repeated