Posts
5622Following
353Followers
552NEPŘÁTELSKÉ EMOCE 🇺🇦🇨🇿
lkundrak@metalhead.clubbreaking: white house being replaced by a white trailer park
Jarkko Sakkinen
jarkkoJarkko Sakkinen
jarkkoFor VM/embedded images socat is pretty alternative to curl as it has 50% less dependencies and you can still web e.g.,
printf 'GET / HTTP/1.1\r\nHost: www.iki.fi\r\nConnection: close\r\n\r\n' | socat OPENSSL:www.iki.fi:443 -
I’ve replaced curl with socat in my BuildRoot images for kernel testing because it is less bloated than curl ;-)
Jarkko Sakkinen
jarkkoBasing immutablity to a label makes crates.io quite unrobust IMHO, and given that not all projects fly that far, otherwise useful labels stay reserved permanently, up until Sun melts.
Such dual-name scheme could be transparent to Cargo.toml: e.g. Cargo.lock could map a label to a name.
I'm not saying that names would need to have expiration time. I'm thinking more like willingly giving name back to circulation from abandoned project.
C++ has bunch of offerings now for cargo alike package managers. In that front, I'd try to find a solution that is smarter than Cargo before there is a dominating solution.
#rustlang #cargo
Jarkko Sakkinen
jarkko[1] https://git.kernel.org/pub/scm/linux/kernel/git/jarkko/tpm2-protocol.git
Jarkko Sakkinen
jarkkoJarkko Sakkinen
jarkkohttps://git.kernel.org/pub/scm/linux/kernel/git/jarkko/tpm2sh.git/tree/src/wildcard.rs?h=main
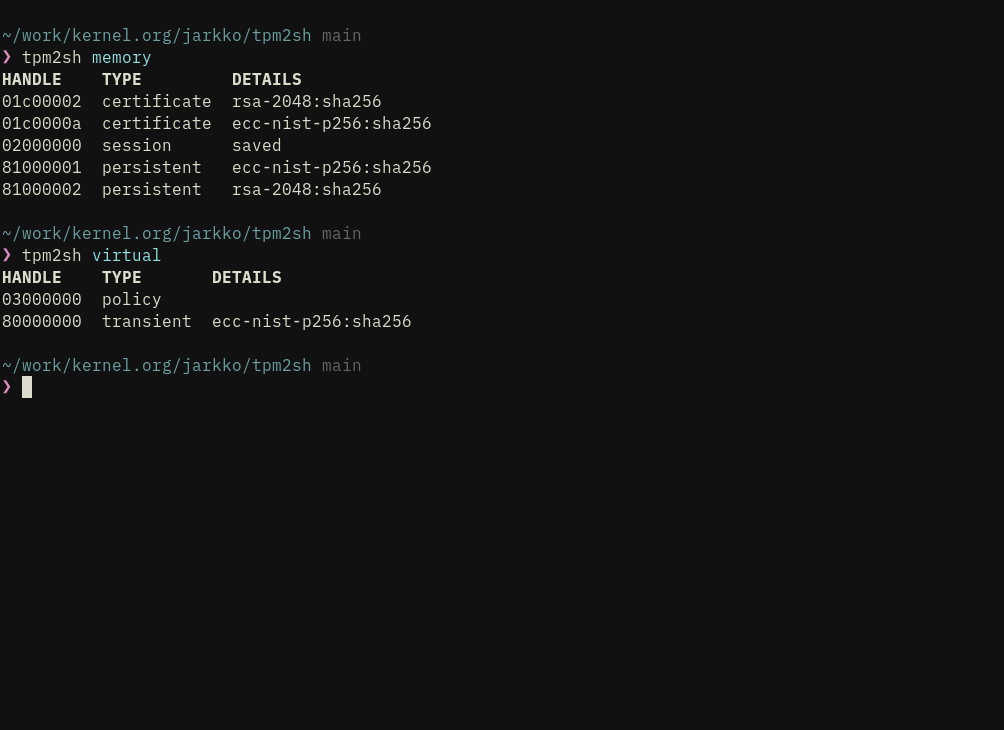
made a little wildcard parser last night so that I don’t have to implement docker esque “tpm2sh reset” command.
e.g. cache can be reseted now by tpm2sh delete 'vtpm:*'
Jarkko Sakkinen
jarkkohttps://crates.io/crates/tpm2sh
#linux #rustlang #tpm
Jarkko Sakkinen
jarkkoJarkko Sakkinen
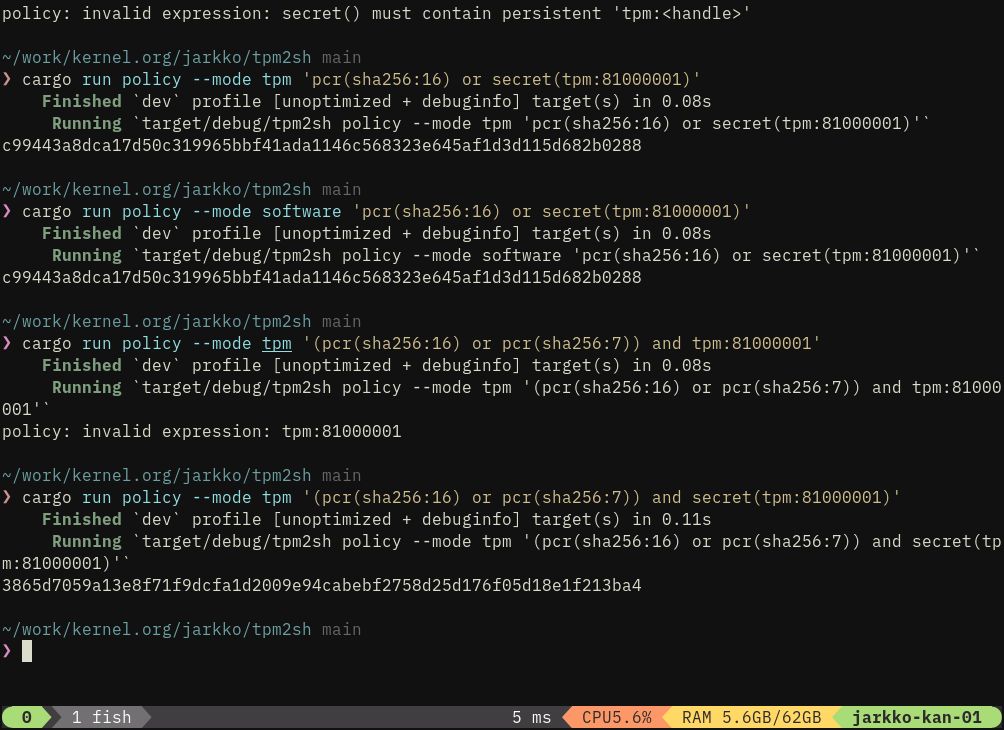
jarkkoI’m planning to iteratively make tpm2sh policy subcommand to compile policy expressions first into eBPF i.e., --mode ebpf option.
We can use this to address bottleneck in trusted keys in kernel: TPMKey ASN.1 provides key blob but not steps how to create policy session that authorizes the key.
Today: TpmKey ASN.1 with auth value and policy digest can be passed but really only auth value (+ PCR selection in TPM2_Create) can be used for authentication.
My vision for policy protected keys is basically:
- Key data is passed as TPMKey ASN.1 just like today.
- In addition eBPF program for creation policy session is passed when policy digest is used.
It’s perfectly secure given that a malicious eBPF program would end up to a different policy digest than what is associated with the key.
Jarkko Sakkinen
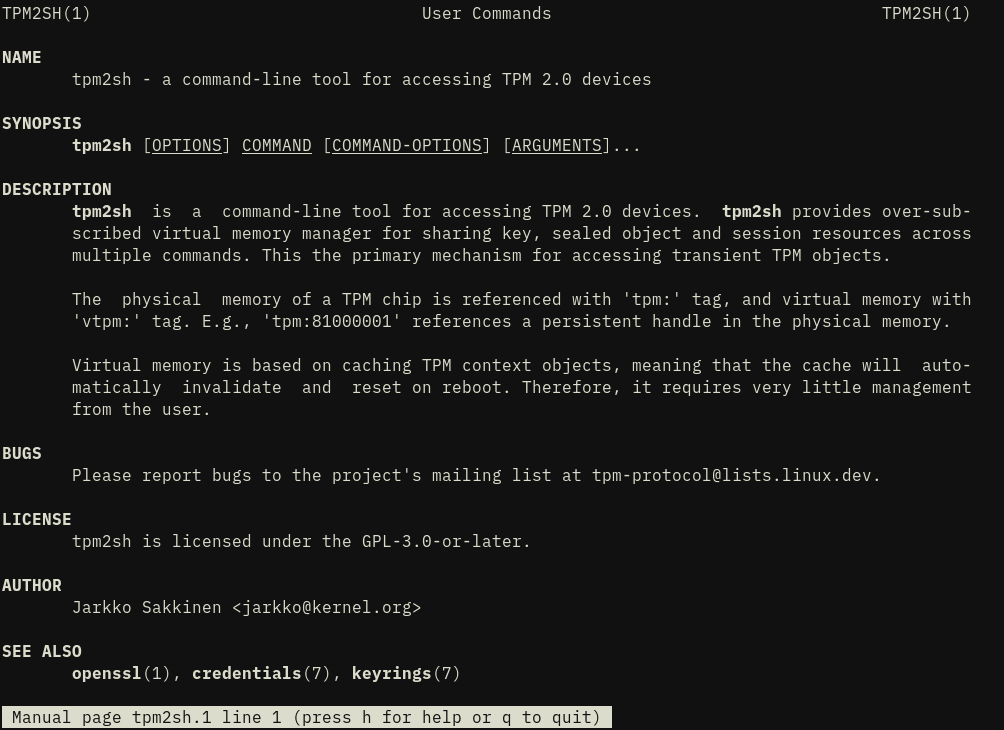
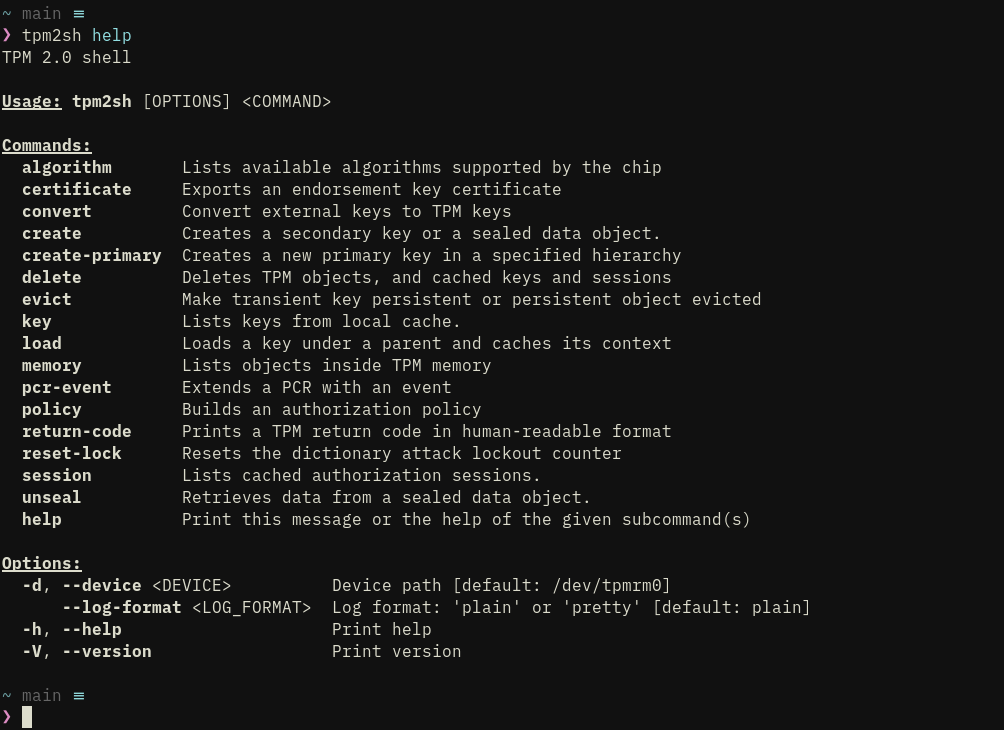
jarkkotpm2sh 0.11.16
This is the release where things mostly work and is first usable version for wider audience than just me.
Functionality is focused on key management and it is quite limited on operations.
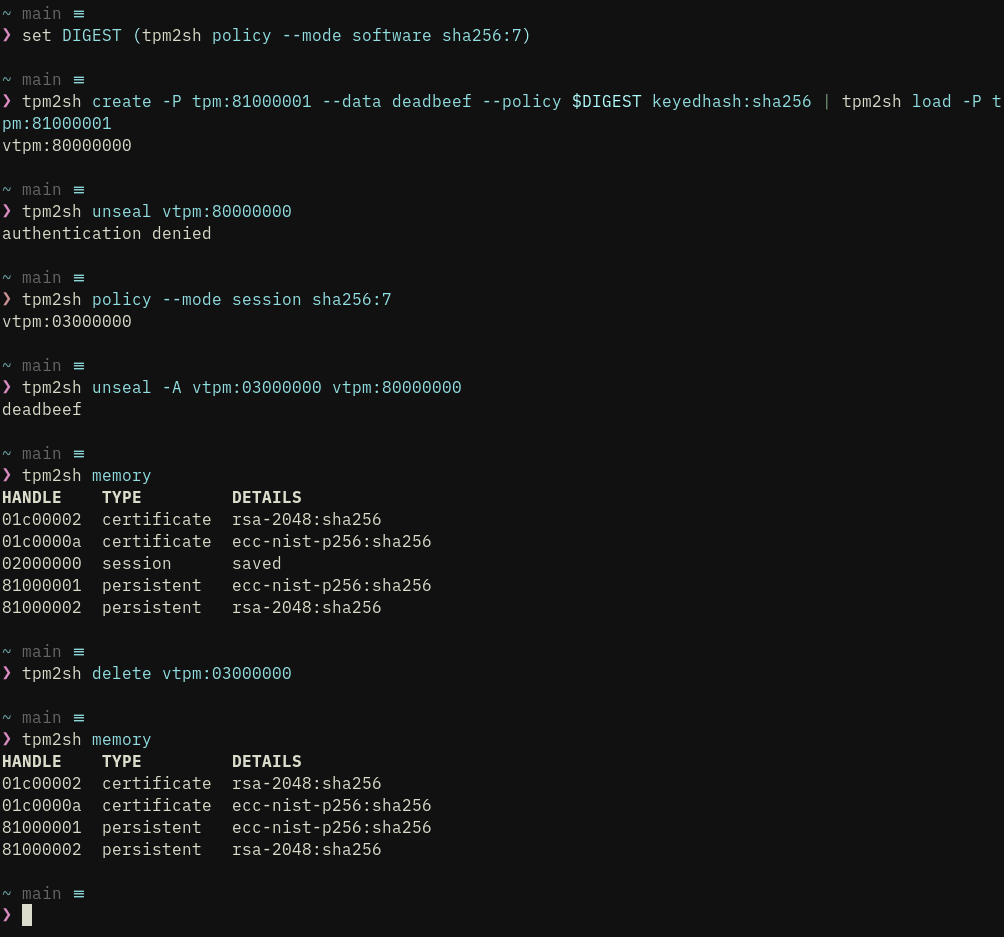
That said, it the most important functionalities, and most difficult to implement, in place:
- Implicit creation of HMAC sessions to protect communication, and hiding its complexity . It is still a stub as parameter encryption is not in place but the mechanism is working correctly.
- Key management including direct support for PKCS#1, PKCS#8 and SEC1 external keys with custom parsers so that dependencies are light for e.g., BuildRoot embedded/VM targets. 3, Seamless over-subscription with key context cache (in ~/.cache/tpm2sh). Detects stale contexts from previous power cycles. “Cache keys” can be referred bit “key:<hex grip>” type of “URI”, where grip is 8 bytes of the key’s name hash.
- Seamless policy sessions with policy command, which can output both composite digest and session handle.
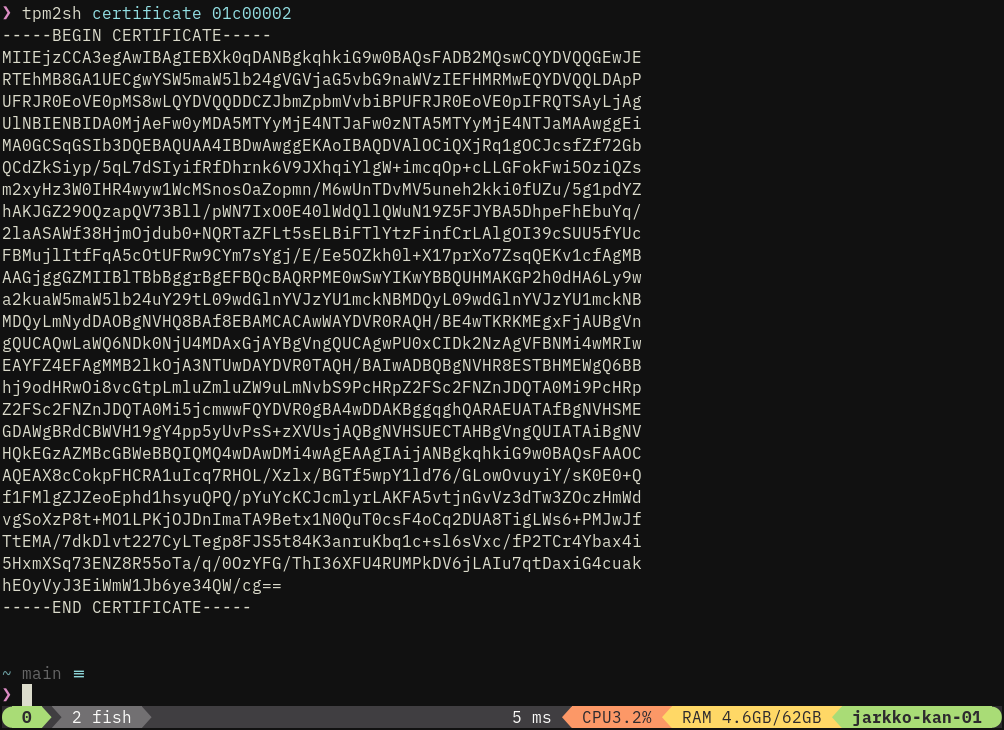
- Intuitive way to download vendor certificates from the chip.
- Full support for the TPMKey ASN.1 format, which is what kernel speaks.
Adding signing etc. ops would have been worse mistake to do before getting this basis right.
It’s not aiming to do all what tpm2-tools does but more like do stuff that I want to do and implementing that as a command-line tool :-) I.