Posts
5624Following
353Followers
552Jarkko Sakkinen
jarkkoit was super-frustating to copy-paste set-and-forget one-time pad answers to questions such as "what was your mothers maiden name", when they were still a thing.
i don't know who invented them but the person should get some kind of worst invention of IT ever award or something.
#infosec #password
Jarkko Sakkinen
jarkkoJarkko Sakkinen
jarkkohttps://git.kernel.org/pub/scm/linux/kernel/git/jarkko/sysdarch.git/
Just though to upload it somewhere for backup.
It has secure boot (sbctl), TPM2 unlock, and finally EXT4, which is probably a twist from current standards (but is so convenient given universal support everywhere).
Jarkko Sakkinen
jarkkorust learning of today: to avoid integer overflows when summing up lengths, always use checked_add in such situations :-)
E.g., this is wrong:
let total_body_len =
handle_area_size + parameter_area_size_field_len + param_area_size + sessions_len;
And this is right:
let total_body_len = handle_area_size
.checked_add(parameter_area_size_field_len)
.and_then(|len| len.checked_add(param_area_size))
.and_then(|len| len.checked_add(sessions_len))
.ok_or(TpmProtocolError::IntegerTooLarge)?;
Jarkko Sakkinen
jarkkoThus, 180 degrees disagreement on bullet 2.
Marko Karppinen
karppinen@mastodon.onlineHeh, Amazon's satellite internet service launched yesterday and their first marketing angle is “how about you get your AWS Direct Connect over satellite instead of paying for cross connects”
https://www.aboutamazon.com/news/amazon-leo/amazon-leo-satellite-internet-ultra-pro
Randahl Fink
randahl@mastodon.socialHere is my Ukraine peace proposal:
1. Putin is sent to The Hague.
2. Russian soldiers leave Ukraine including Crimea.
3. Russia returns all kidnapped Ukrainian children.
4. Russia releases all Ukrainian prisoners.
5. Russia pays damages for everything their war has destroyed.
6. Russia pays damages to Ukrainian families who have lost family members.
7. Russia pays damages to every person who has been tortured, abducted or otherwise criminally mistreated.
8. Ukraine becomes a member of the EU.
Jarkko Sakkinen
jarkkoor it's as hacker enabled as IBM mainframes.
i.e., there is no such thing as distruptive innovation.
it might be commercially viable story for companies that produce the hardware to other big companies but it is still a sad story ;-)
and you do not own the hardware EVEN if you buy it because it's locked in to the CPU companies CA.
Jarkko Sakkinen
jarkkoJarkko Sakkinen
jarkkoYa, looks great!
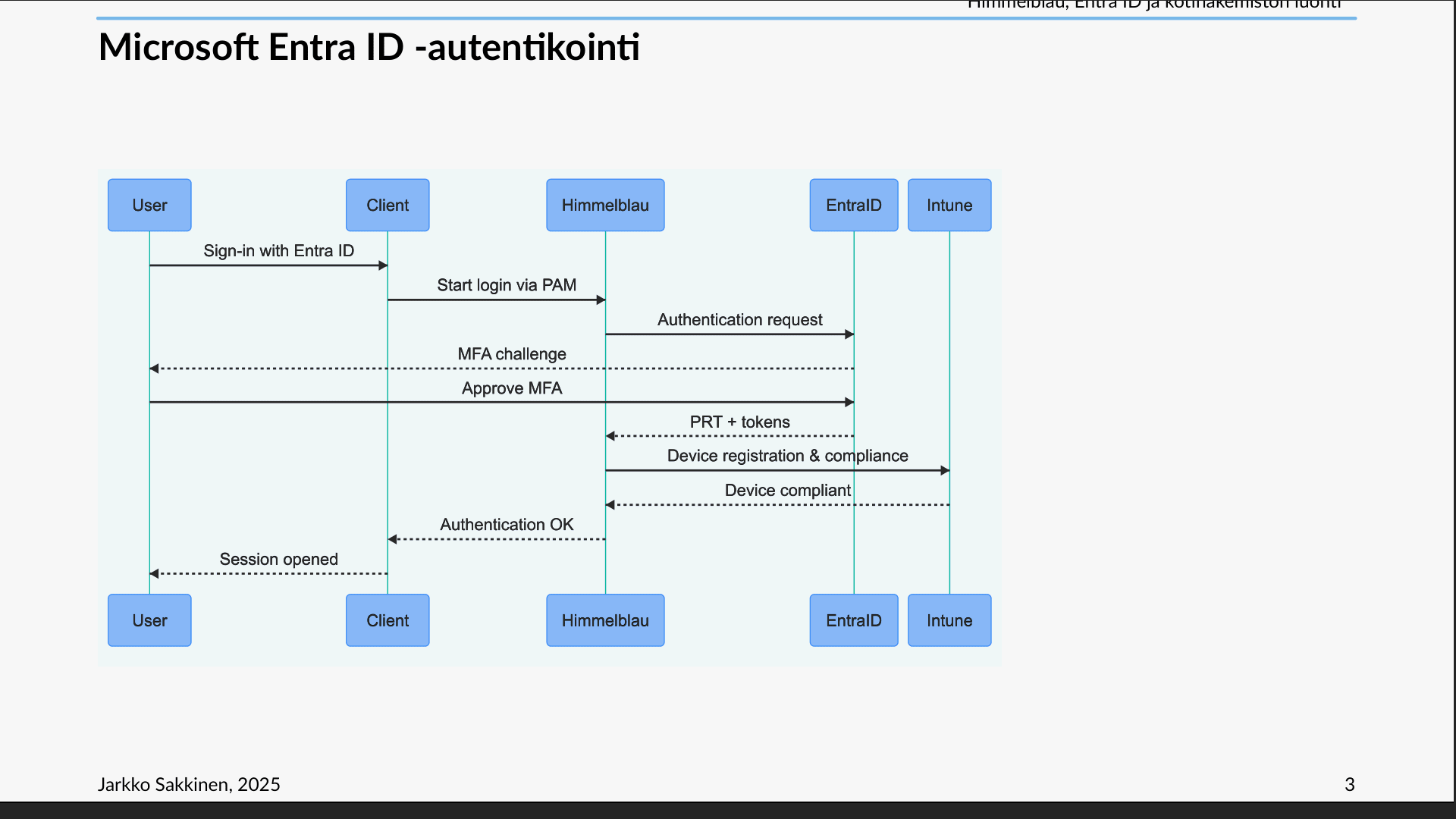
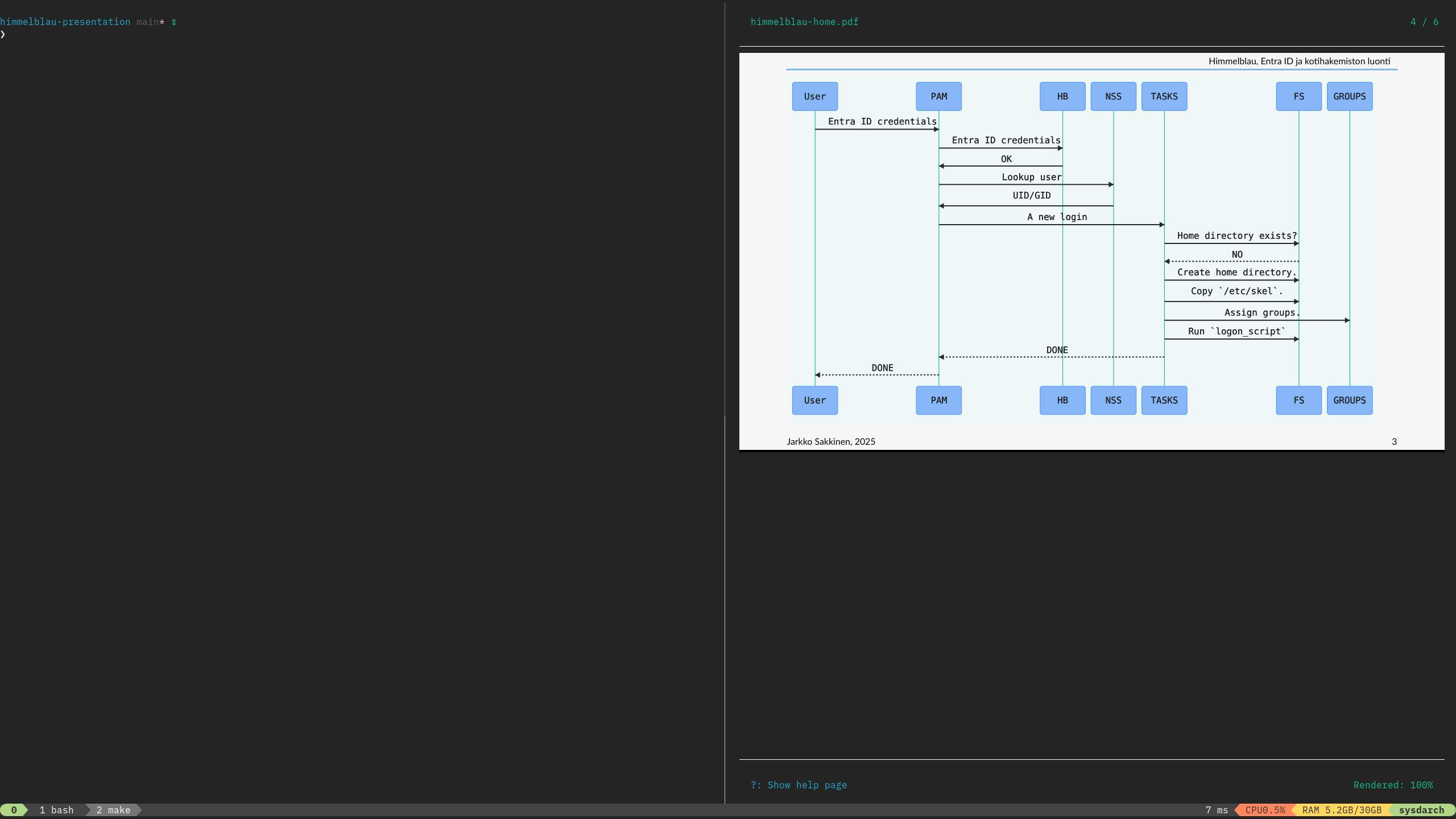
I've started to use this package for Typst called 'pitorita', which allows to do diagrams embedded to the document you should check this out:
https://typst.app/universe/package/pintorita/
IMHO, it's also investment to decks with typst because you get from every presentation bunch of re-usable slides and diagrams :-)
Jarkko Sakkinen
jarkkoJarkko Sakkinen
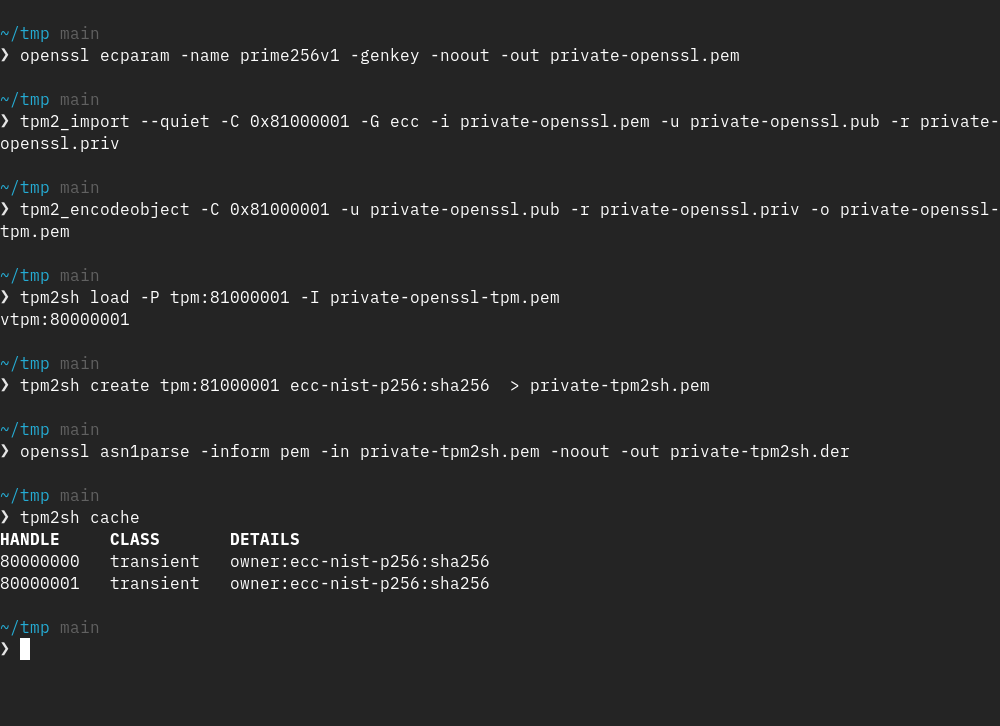
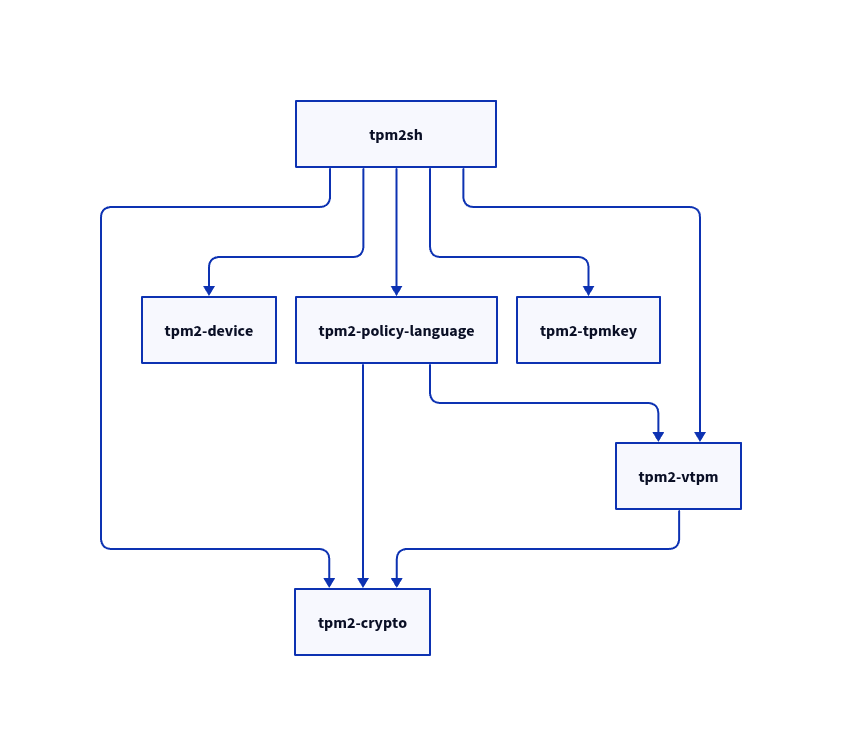
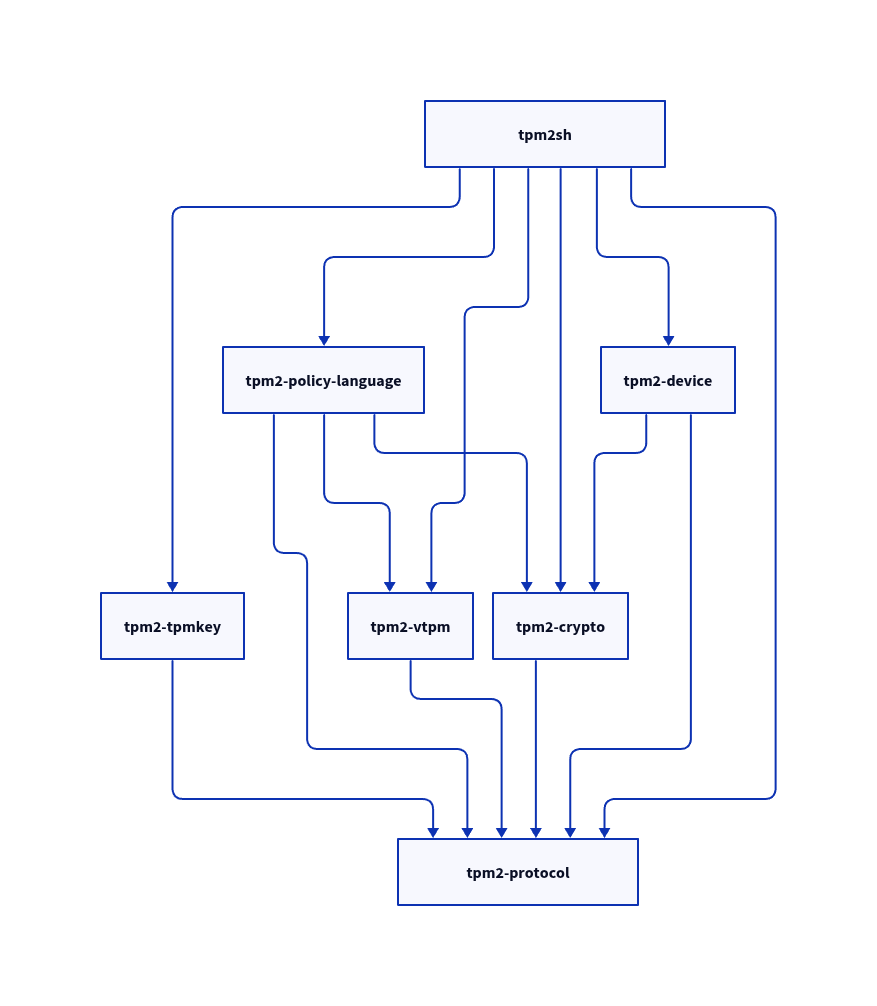
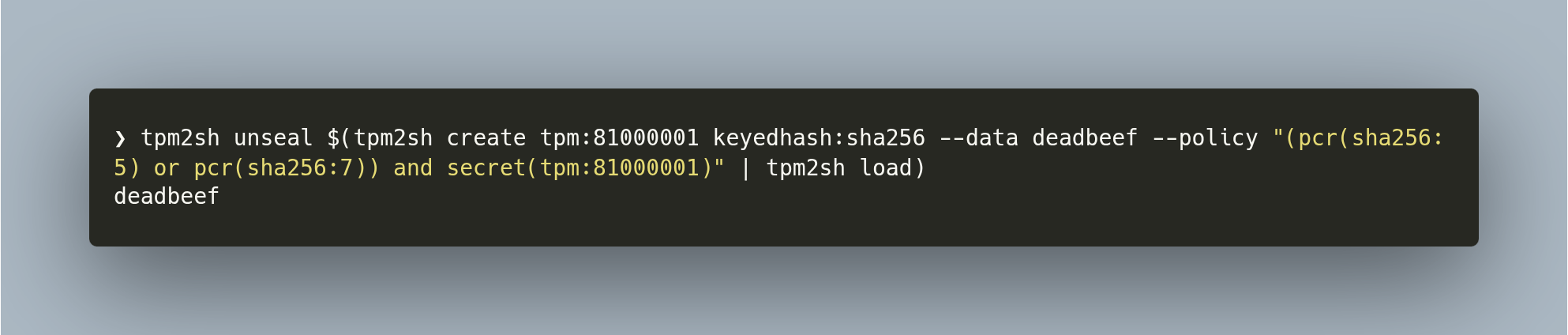
jarkkoStill in very early phases. Now my micro ecosystem has:
1. tpm2-protocol
2. tpm2-crypto (software crypto for doing TPM2 related operations like generating encrypted seeds).
3. tpm2-policy-language
4. tpm2-tpmkey
5. tpm2-vtpm
I think what I get right vs. TSS2 etc. that I'm not building a "big SDK" but instead of common sense re-usable components not enforcing architecture or policy.
#linux #rustlang #tpm
Jarkko Sakkinen
jarkkoJarkko Sakkinen
jarkkoBTW, diagram is also made with Typst.
Greenpeace International
greenpeace@mastodon.social57 companies are responsible for 80% of the global greenhouse gas emissions since 2016.
Unless you run those companies, why are you being forced to pay for climate change damage?