Posts
440Following
101Followers
4731Matthias Endler
mre@mastodon.socialNew live episode of Rust in Production and it's a special one! 🥁
Recorded on stage at Rust Week in Utrecht with two people shaping the future of the Linux kernel:
🐧 Greg Kroah-Hartman (@gregkh ), Linux Foundation Fellow
⚙️ Alice Ryhl, core maintainer of Tokio, Rust for Linux at Google
▶️ https://corrode.dev/podcast/s06e04-rust4linux/
Huge thanks to the Rust Week crew for hosting this one. You're awesome! 🦀
First talk of the day with Greg @gregkh KH to talk about Untrusted data in in Linux : How Rust is going to save us.
I'm at the recording for the Rust In Production podcast on "Oxidizing the Linux Kernel" with Greg @gregkh KH, Alice Rhyl and Matthias @mre Endler.
#RustWeek #RustWeek2026 #LinuxKernel #RustLang #RustForLinux
Greg K-H
gregkhhttps://2026.rustweek.org/schedule/tuesday/
Live streams of the conference:
https://www.youtube.com/@rustnederlandrustnl/streams
I think the podcast might be streamed here as well:
https://www.youtube.com/playlist?list=PLbWDhxwM_45lkJfL95zELDgO01mnrRQ6t
but don't really know...
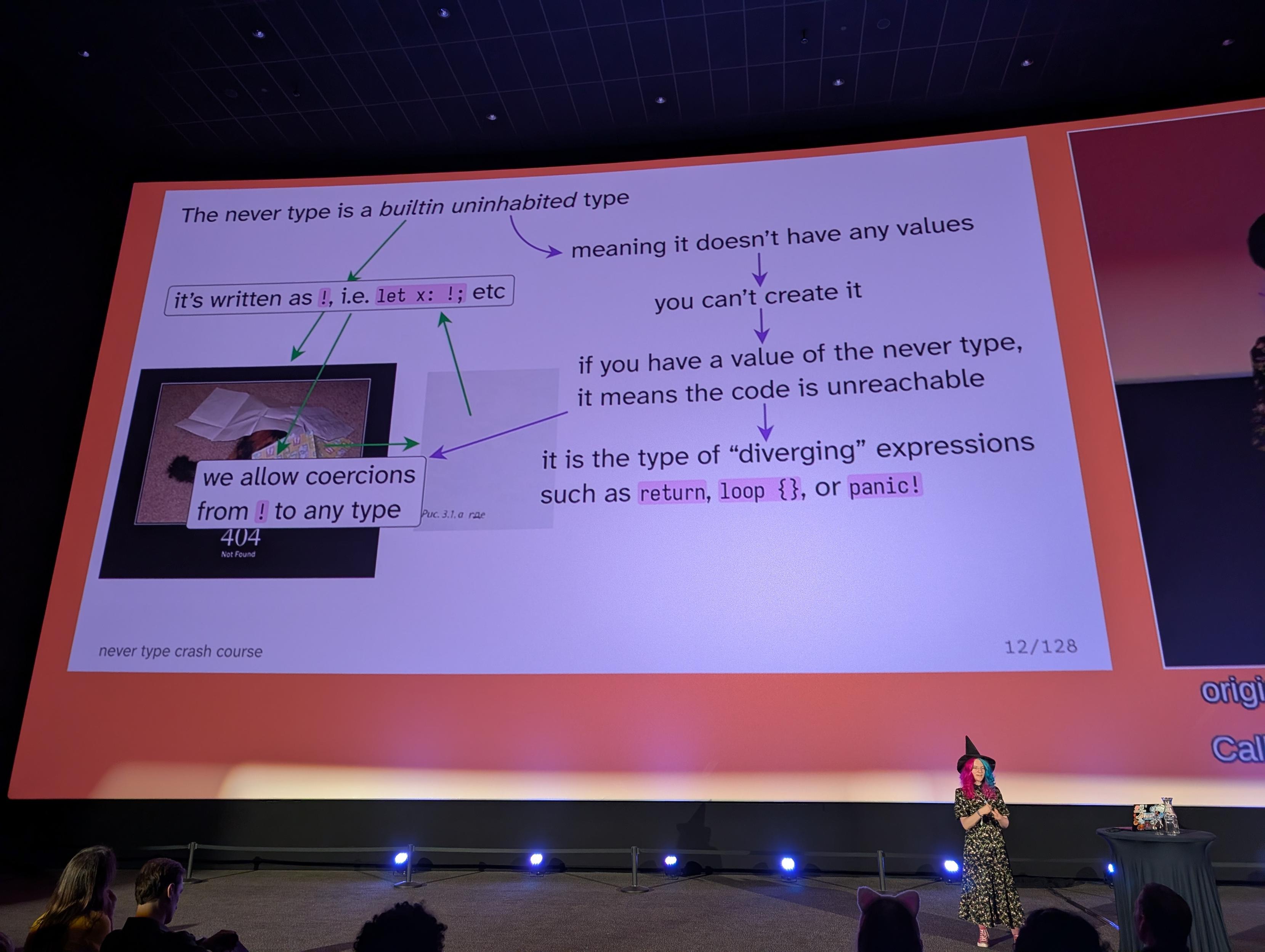
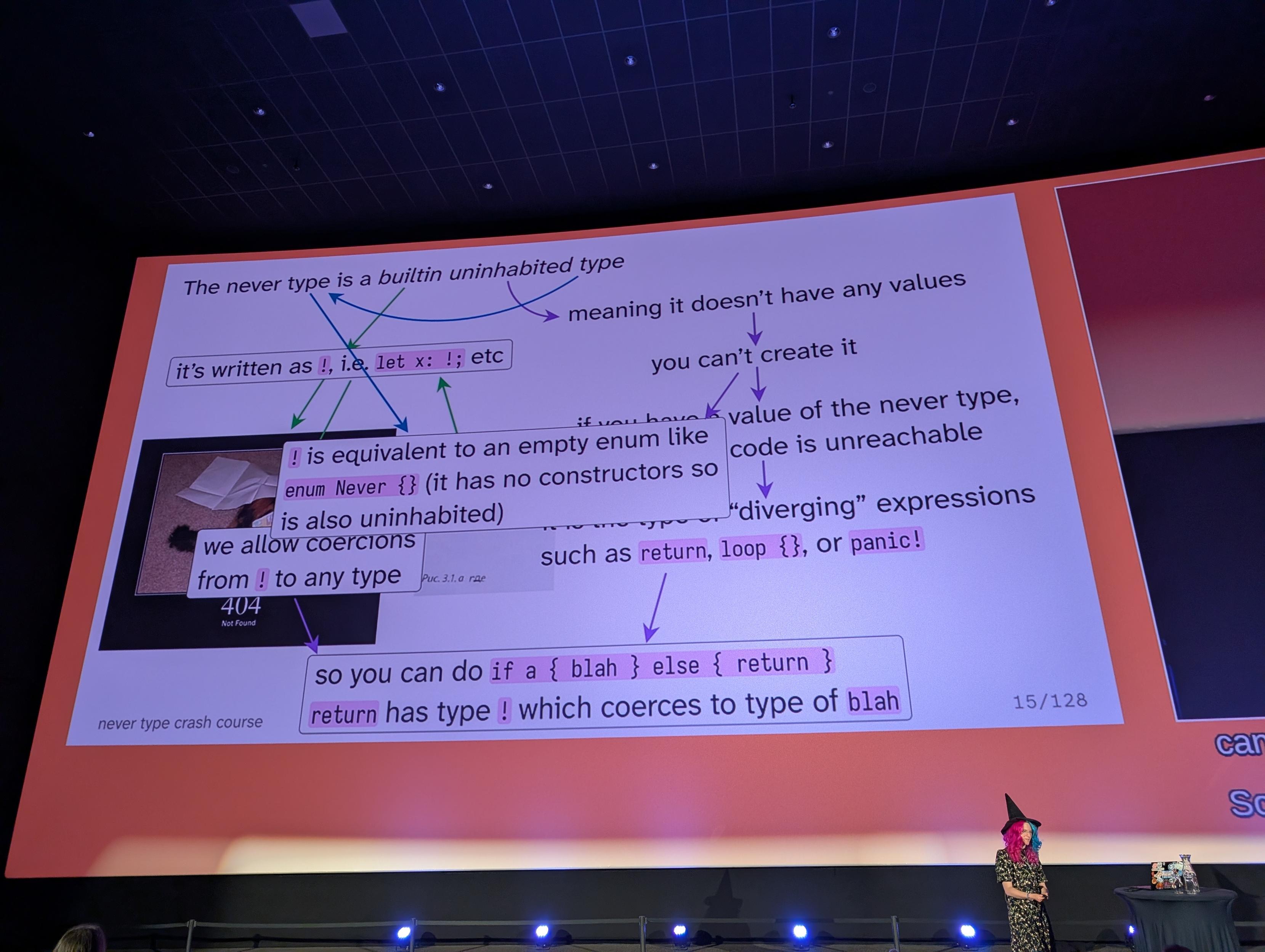
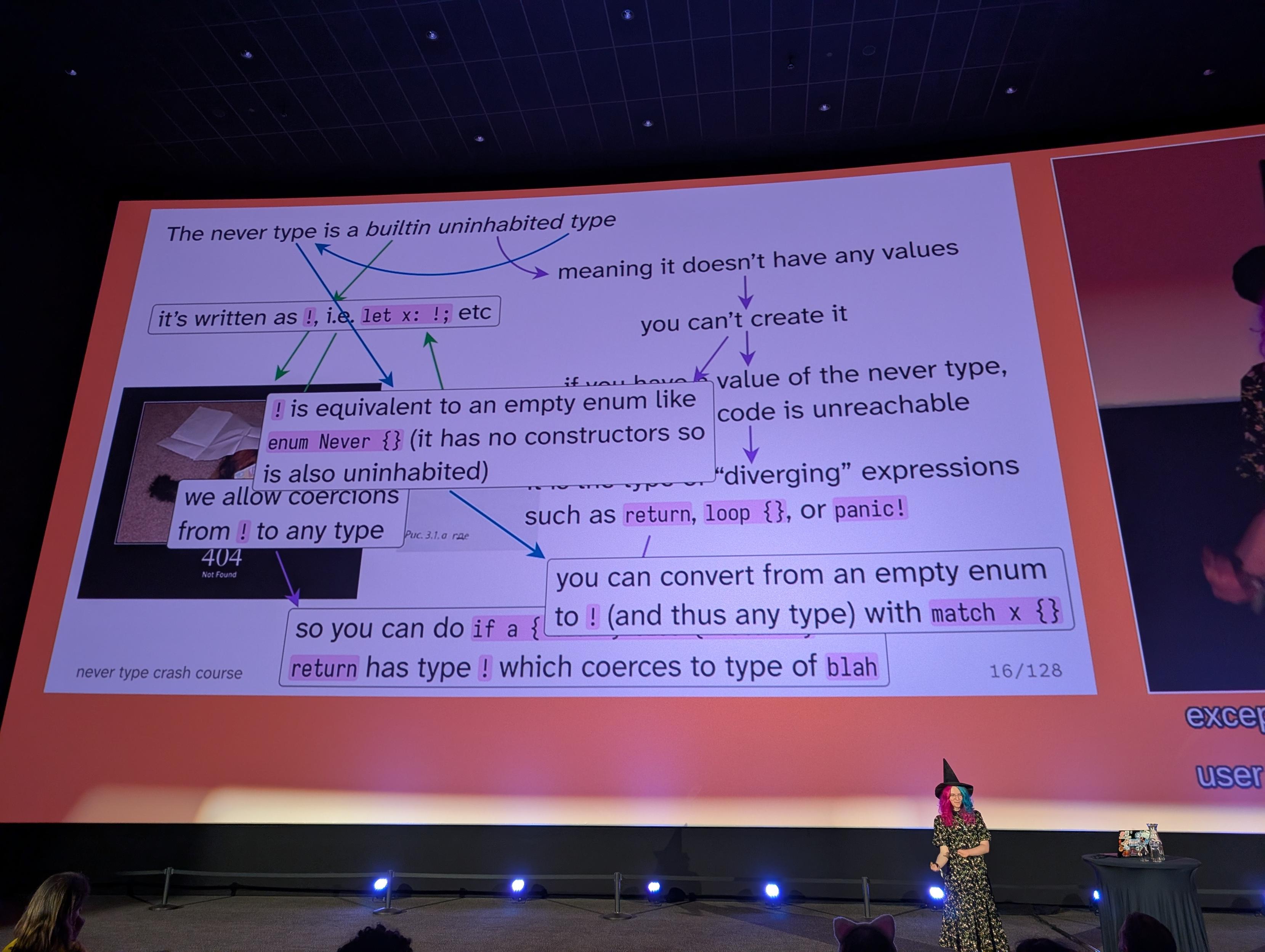
What is never? It's a Rust type that's pretty simple to define (not).
Greg K-H
gregkh"If Linux can be maintained by sending patches to an email mailing list, 'doesn’t work at scale' arguments are skill issues."
https://dbushell.com/2026/04/29/github-is-sinking/
Hoshino Lina (星乃リナ) 🩵 3D Yuri Wedding 2026!!!
lina@vt.socialTypical ML argument: "If I can read something legally, why can't I train an LLM on it?"
Humans are capable of reading things and later writing a similar thing that is still a copyright violation. If I go and write a book that follows the plot line of Star Wars, that's still a copyright violation, even if no text is literally the same. If I play the melody to a song on my piano and release it without the appropriate mechanical cover license, that's also a copyright violation.
The reason this does not happen often is that, as humans, we are aware that that's plagiarism and there are rules. Sometimes it happens by accident, and people still get sued and lose.
LLMs have no such awareness and routinely output things which are blatant copyright violations when appropriately prompted. That means the model weights encode that work, and therefore, are themselves a derivative work.
Your brain encodes a massive amount of copyrighted information. You are not a walking copyright violation because humans aren't data, can't be copied and distributed en masse, have human rights, etc. This is why "mind reading machines" are a classic dystopian plot point (monetizing your thoughts etc).
An LLM is not a human, does not have human rights, nor human privileges. It is data, and if it encodes copyrighted information, that's a derivative work. If you aren't following the license of the training data, that's a copyright violation.
daniel:// stenberg://
bagder@mastodon.social@dascandy everything graphed risks becoming a goal in itself, so I make sure we graph everything 😀
Greg K-H
gregkhAnd again, my point remains, "All early release lists leak like a sieve, otherwise why does your government allow it to exist."
Greg K-H
gregkhSee how it breaks down when it hits the real world?
As I have said many times, "All early-announce lists are a leak, otherwise why would your government allow it to exist?"
Greg K-H
gregkhGreg K-H
gregkh"The Kernel assigns lots of CVEs. They say it’s because they don’t really know how the Kernel is being used, so they err on the side of caution. Companies hate this because they have to deal with a lot of CVEs. Does the Kernel do this because it’s easier or do they have some sort of secret nefarious reason? Probably because it’s just easier and they have zero downside to disclosing and moving on. "
RE: https://infosec.exchange/@joshbressers/116507930206819253