Posts
440Following
101Followers
4731Matthew Garrett
mjg59@nondeterministic.computer"Linux would have prevented this!" literally true because my former colleague KP Singh wrote a kernel security module that lets EDR implementations load ebpf into the kernel to monitor and act on security hooks and Crowdstrike now uses that rather than requiring its own kernel module that would otherwise absolutely have allowed this to happen, so everyone please say thank you to him
binbows@labyrinth.zone
binbows@labyrinth.zoneit's YOUR day!
ruin it yourself by attempting a gentoo install
Gustavo A. R. Silva 
gustavoars@fosstodon.org
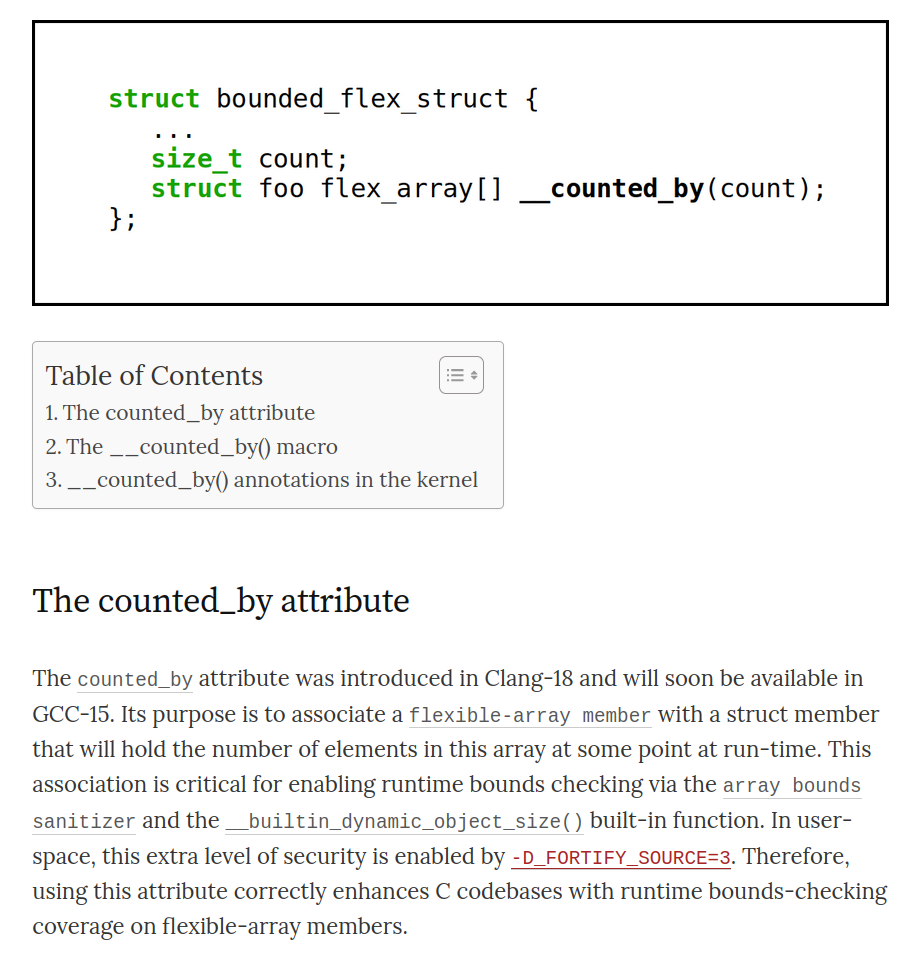
I just wrote a blog post about how to use the new counted_by attribute in C and the Linux kernel. I've been mentioning this attribute in my presentations over the past year, and I thought it was about time to write about it. So, here you go:
"How to use the new counted_by attribute in C (and Linux)"
https://embeddedor.com/blog/2024/06/18/how-to-use-the-new-counted_by-attribute-in-c-and-linux/
I hope you find it useful. Thanks!
Kernel Self-Protection Project ⚔ 🛡 🐧
Greg K-H
gregkhRE: https://mastodon.nl/@bert_hubert/112608731406238492
Bert Hubert NL 🇺🇦🇪🇺🇺🇦
bert_hubert@mastodon.nlOver vorige post, je kan ook zeggen dat het kabinet "geen grip heeft op de migratie" (naar de cloud). https://berthub.eu/articles/posts/de-hele-overheid-naar-de-cloud-dat-is-een-politiek-besluit/
Thorsten Leemhuis (acct. 1/4)
kernellogger@fosstodon.orgJeremy Allison writes:
'" The data shows that “frozen” vendor #Linux kernels, created by branching off a release point and then using a team of engineers to select specific patches to back-port to that branch, are buggier than the upstream “stable” Linux #kernel created by Greg Kroah-Hartman. '"
https://ciq.com/blog/why-a-frozen-linux-kernel-isnt-the-safest-choice-for-security/ #LinuxKernel
Programming Quotes
programming_quotes@mastodon.socialGet out of the way of your developers or lose them to someone who will.
— Adrian Cockcroft
Mike Dolan
mdolan@fosstodon.orgI just got a few ideas for the next idiotic #opensource DMCA takedown notice I have to respond to...
mxk
mxk@hachyderm.io"hi I am Greg, this is wrong, everything I say is public information and *not* under NDA" - @gregkh on stage of the #GoogleAndroidBootcamp
LWN.net is now @LWN@lwn.net
LWN@fosstodon.orgSaturday's stable kernel updates https://lwn.net/Articles/969732/ #LWN
LWN.net is now @LWN@lwn.net
LWN@fosstodon.orgFour stable kernel updates https://lwn.net/Articles/969352/ #LWN
Krzysztof Kozlowski
krzkEOSS: https://sched.co/1aBEf
OSSNA: https://sched.co/1aPvr
Thomas Depierre
Di4na@hachyderm.ioWell, I finally have data to back my model of the software world out there. And the data is relatively solid and shows what I keep saying.
You are all on our turf now. Please accept that you have no idea what you are talking about. Sit down. Listen. Ask questions.
But respect our work. We are trying to keep the world running, 1h per month.
https://www.softwaremaxims.com/blog/open-source-hobbyists-turf
LWN.net is now @LWN@lwn.net
LWN@fosstodon.orgEight new stable kernels https://lwn.net/Articles/966755/ #LWN
Tweakers
Tweakers@mastodon.socialMinister Adriaansens: verhuizing SIDN naar Amazon 'nog geen voldongen feit' https://tweakers.net/nieuws/220102/minister-adriaansens-verhuizing-sidn-naar-amazon-nog-geen-voldongen-feit.html
Greg K-H
gregkhLinux Kernel Ecosystem" in which different distros, and Android, are evaluated as to how up to date they stay with upstream fixes. Note that RHEL or CentOS is not evaluated "because of the lack of public git repositories or insufficient data."
About time someone started writing papers about this stuff...
Omkhar
Omkhar@infosec.exchangeWe're #hiring at the @openssf !
Our mission is to ensure the security of open source software for all.
Are you a seasoned Technical Program Manager excited about #cybersecurity and #opensource who wants a full-time #remotejob?
Apply: https://openssf.jobboard.io/jobs/314008394-technical-program-manager-at-openssf
K. Ryabitsev-Prime 🍁
monsieuriconThorsten Leemhuis (acct. 1/4)
kernellogger@fosstodon.orgDid a quick *rough* check:
* 65 #Linux #kernel CVE announcements from Greg so far
* 55 of those refer to a mainline commit
* 10 of those were marked for backporting to stable/longterm
And that's why Greg backports a lot of #LinuxKernel mainline commits to stable/longterm that are *not* tagged for backporting -- and why "only backport changes mainline developers[1] tagged for backporting" is a bad idea.
[1] reminder, such tagging is optional, as participation in stable/longterm is optional
sjvn
sjvn@mastodon.socialThe #Linux kernel developers are now issuing their own, more accurate Common Vulnerabilities and Exposures #security bulletins. https://opensourcewatch.beehiiv.com/p/linux-gets-cve-security-business by @sjvn
The Linux kernel developers are now in charge of its Common Vulnerabilities and Exposures (CVE) security problems.