Posts
440Following
101Followers
4736Thorsten Leemhuis (acct. 1/4)
kernellogger@fosstodon.org#Linux 6.11 is out:
https://lore.kernel.org/lkml/CAHk-=whVpSHw9+4ov=oLevfv8sPYbh59T_9VKif-6Vqkr41jQA@mail.gmail.com/
'"I'm once again on the road and not in my normal timezone, but it's Sunday afternoon here in Vienna, and 6.11 is out.
The last week was actually pretty quiet and calm, which is nice to see. […]
Anyway, with this, the merge window will obviously open tomorrow, and I already have 40+ pull requests pending. That said, exactly _because_ I'm on the road, it will probably be a fairly slow start […] please be patient."'
Greg K-H
gregkhhttps://lore.kernel.org/all/20240913112643.542914-1-benno.lossin@proton.me/
It's not a "silver bullet" for why we should be using rust in the Linux kernel, but it is a "big giant sledgehammer" to help squash and prevent from happening MANY common types of kernel vulnerabilities and bugs (remember, "all input is evil!" and this change forces you to always be aware of that, which is something that C in the kernel does not.)
I had always felt that Rust was the future for what we need to do in Linux, but now I'm sure, because if we can do stuff like this, with no overhead involved (it's all checked at build time), then we would be foolish not to give it a real try.
And yes, I've asked for this for years from the C developers, and maybe we can also do it there, but it's not obvious how and no one has come up with a way to do so. Maybe now they will have some more incentive :)
Jani Nikula
jani@fosstodon.orgMust not make a comparison. Really. Must not. But just saying...
Clang Built Linux took literally years of effort. And it's all still C, just a different compiler.
Did anyone really expect Rust for Linux to be a breeze?
I know, I know, apples and oranges.
🐧sima🐧
sima@chaos.socialkangrejos in copenhagen was great, but the absolute 🤯 moment was when I learned that GFP_ stands for get_free_pages
I had no idea. and @gregkh next to me had the same https://xkcd.com/1053/ experience
Paul Moore
securepaul@fosstodon.orgAnyone else often find themselves starting a retort/reply to a thread here, only to abandon the effort part way through, because you realize your time is better spent supporting/fixing/making things than trying to educate people who haven't bothered to do any of the most basic level of self-education on the given topic?
Greg K-H
gregkhhttps://lore.kernel.org/all/TYUPR06MB6217E6BD48B0B491AA169E67D29D2@TYUPR06MB6217.apcprd06.prod.outlook.com/
Greg K-H
gregkhhttps://git.sr.ht/~gregkh/usbutils/commit/86dcab8964901d15b87b156546559c8ae28bd9fe
jelly
jelly@dodgy.downloadNew blogpost about creating bit-by-bit reproducible images with mkosi(!)
https://vdwaa.nl/mkosi-reproducible-arch-images.html
#archlinux #systemd #mkosi
K. Ryabitsev-Prime 🍁
monsieuriconMe: "Oh, yeah, for sure."
Greg K-H
gregkhKernel source is all public (there's a 6.1.y and 6.6.y tree at the moment), hopefully will start working on getting it all merged upstream to make it a proper platform for others to use.
Thorsten Leemhuis (acct. 1/4)
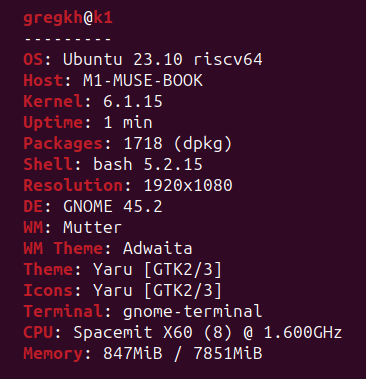
kernellogger@fosstodon.orgI'd really like to read a well researched article that sums up how Linux distros reacted to the massive influx of #Linux #kernel CVE that started ~half a year – both for their #LinuxKernel packages and their live-patching offerings.
But I guess that is an enormous amount of work that no media outlet in this world is willing to pay anyone for writing. 😕
Slide taken from @gregkh's "Why are there so many kernel CVEs?" talk he gave at OSS China yesterday (https://social.kernel.org/objects/c9979d9f-399f-428b-ac56-c41598076dfa ) #LinuxKernel
sjvn
sjvn@mastodon.socialDon't panic! It's only 60 Linux CVE security bulletins a week https://zdnet.com/article/dont-panic-its-only-60-linux-cve-security-bulletins-a-week/ by @sjvn
Sure, it sounds like a lot, but it's just business as usual for #Linux #security.
Greg K-H
gregkhhttps://kccncossaidevchn2024.sched.com/event/ed2b39a9a0cdfc1df18de67ce0c2f6be
Link to git repo for the slides if the schedule site acts odd for you:
https://git.sr.ht/~gregkh/presentation-security
It was fun, and will be the "set up" for my Kernel Recipes talk in Paris in a few weeks (only 3 conferences to go between now and then, travel is back in full swing.)
pabloyoyoista
pabloyoyoista@treehouse.systemsOk, so the day has come. On the context of getting "/usr merge" on alpine, I am going to try update the FHS.
9 years after it was updated, big parts of it are out-of-sync with the current Linux distro conventions.
We (@postmarketOS) already pinged the @linuxfoundation about it in February, and their suggestion was to get somebody interested to do the work. So let's start that process now! Since the FHS mailing list seems defunc (I subscribed and sent an email in February that never got added to the archive), please send me an email at pabloyoyoista@postmarketos.org so we can get a list of people to start discussing the process
#linux #distros #debian #fedora #alpinelinux #postmarketOS #systemd
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@fosstodon.orgRecently, a Dutch hacker found a vulnerability allowing him to shut down 4 million solar power installations. A handful of mostly non-European places manage perhaps 100 GW of solar power in the EU. Any mishap there, or heaven forbid, a compromise, could easily shut down so much power that the European electricity grid would collapse. Shockingly, we regulate these massive control panels as if they are online birthday calendars. And that must change. https://berthub.eu/articles/posts/the-gigantic-unregulated-power-plants-in-the-cloud/
Thomas Depierre
Di4na@hachyderm.ioI think I finally found out why it feels like CISA live on Alpha Centauri.
> “It’s a myth,” she declared, “that software vulnerability is an inevitability. … It’s the same classes of defects we’ve known about for decades and known how to fix for years.”
This is both true and utterly wrong. It is true, we know how to detect and fix them for decades. In research.
But you know what we do not have? Industry tool that can be used in the industry based on this knowledge.
Matthew Garrett
mjg59@nondeterministic.computer"Linux would have prevented this!" literally true because my former colleague KP Singh wrote a kernel security module that lets EDR implementations load ebpf into the kernel to monitor and act on security hooks and Crowdstrike now uses that rather than requiring its own kernel module that would otherwise absolutely have allowed this to happen, so everyone please say thank you to him
binbows@labyrinth.zone
binbows@labyrinth.zoneit's YOUR day!
ruin it yourself by attempting a gentoo install
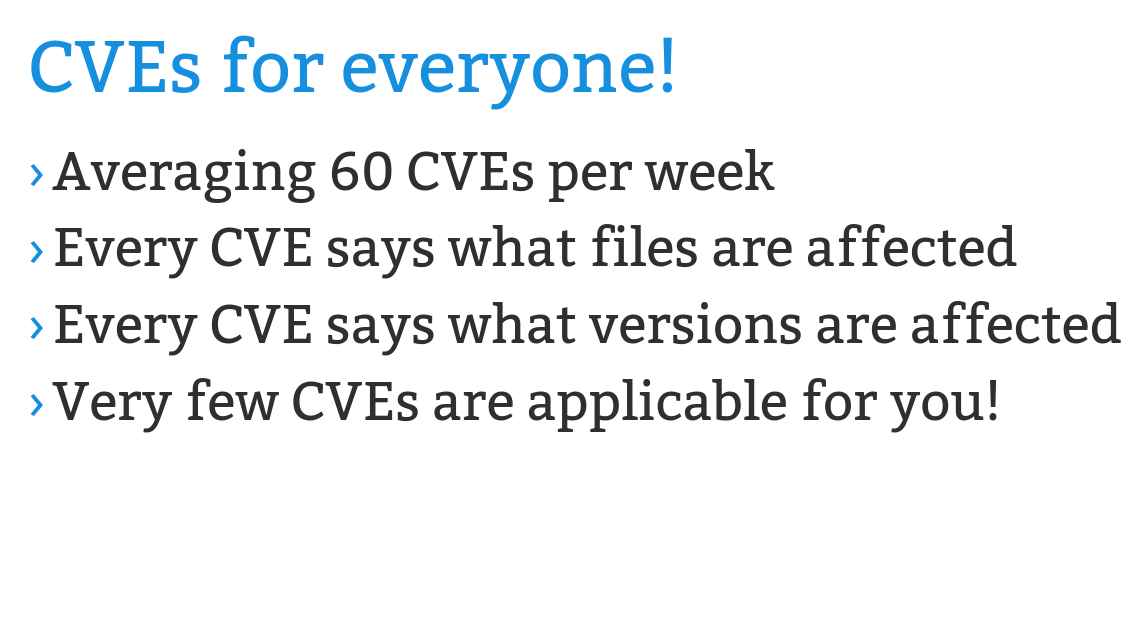
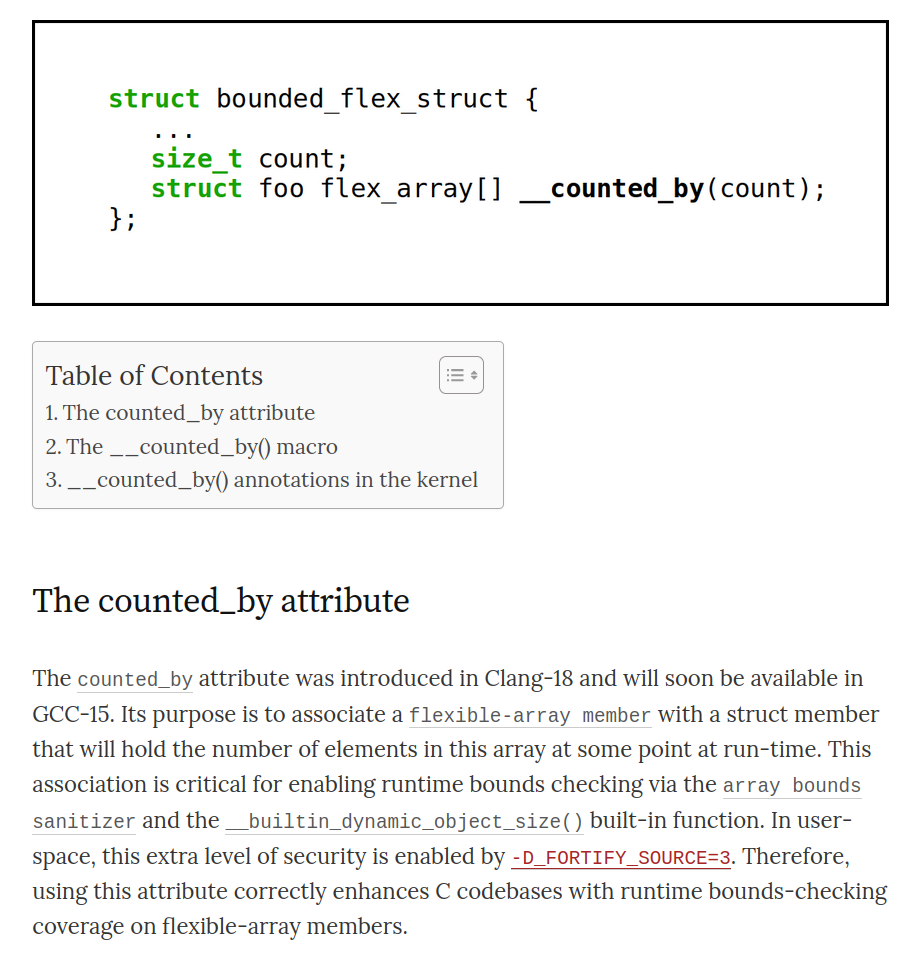
Gustavo A. R. Silva 
gustavoars@fosstodon.org
I just wrote a blog post about how to use the new counted_by attribute in C and the Linux kernel. I've been mentioning this attribute in my presentations over the past year, and I thought it was about time to write about it. So, here you go:
"How to use the new counted_by attribute in C (and Linux)"
https://embeddedor.com/blog/2024/06/18/how-to-use-the-new-counted_by-attribute-in-c-and-linux/
I hope you find it useful. Thanks!
Kernel Self-Protection Project ⚔ 🛡 🐧