Posts
5475Following
346Followers
542Jarkko Sakkinen
jarkko
3rd PR for 6.19: https://lore.kernel.org/linux-integrity/aSthHCovbsDZANsa@kernel.org/T/#u
at least i'm on schedule this time :-)
at least i'm on schedule this time :-)
Jarkko Sakkinen
jarkkoThis is how I manage my pull requests ATM (creating and pushing signed tags, request-pull etc.):
https://git.kernel.org/pub/scm/linux/kernel/git/jarkko/linux-pull-request.git/tree/?h=main
I’m happy with the tiny jq based templating engine for moustache templates. Has worked surprisingly well.
Jarkko Sakkinen
jarkko
Edited 5 months ago
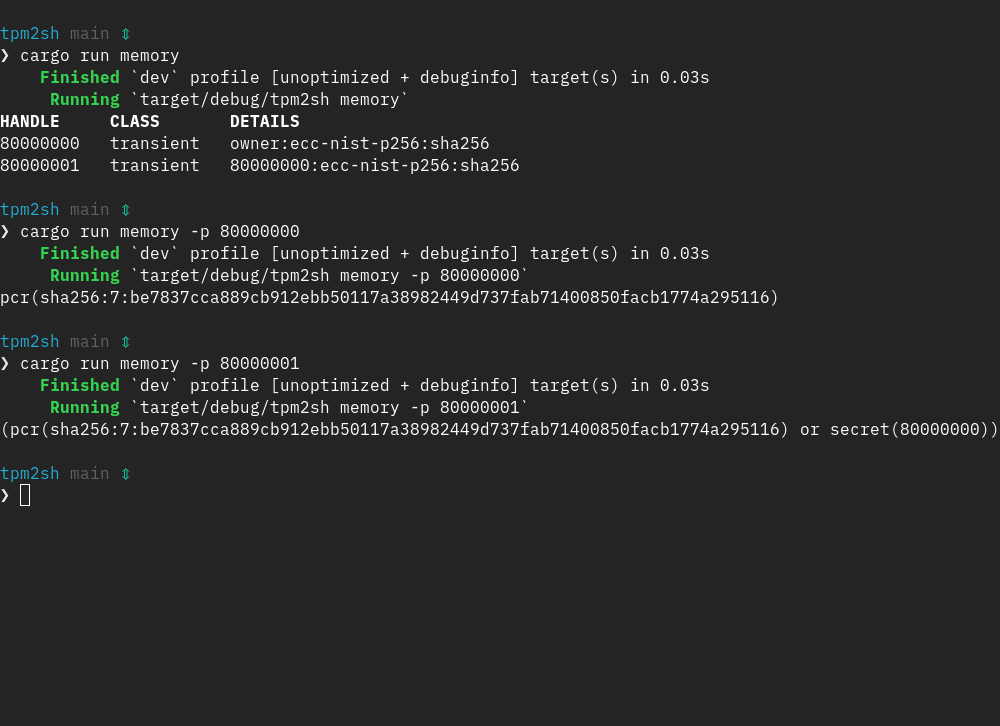
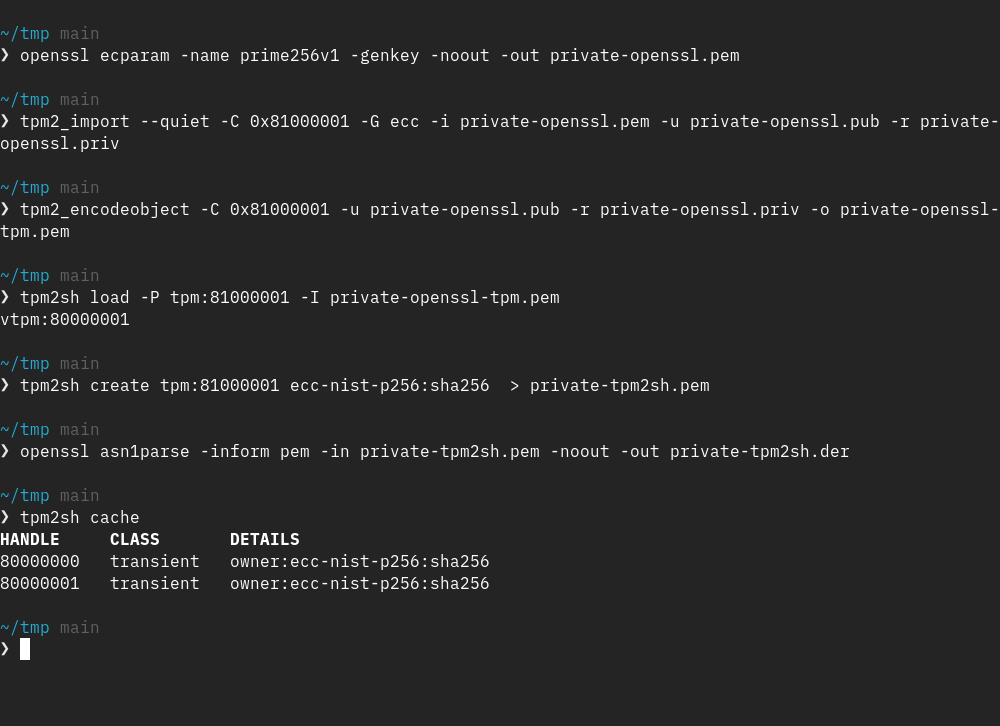
I've been fine-tuning the policy and caching engine in tpm2sh a lot and next version will allow to:
1. View policy as an expression via 'tpm2sh memory -p <handle>'
2. Create primary keys with arbitrary policies (was not just done nothing special in it).
3. Creating, viewing and maintaining policies for persistent keys.
These sort of come as "side-effect" of just cleaning up and polishing the groundwork :-)
#linux #tpm #rustlang
1. View policy as an expression via 'tpm2sh memory -p <handle>'
2. Create primary keys with arbitrary policies (was not just done nothing special in it).
3. Creating, viewing and maintaining policies for persistent keys.
These sort of come as "side-effect" of just cleaning up and polishing the groundwork :-)
#linux #tpm #rustlang
Jarkko Sakkinen
jarkko
What are known good workarounds with systemd-creds for situations like this:
https://github.com/himmelblau-idm/himmelblau/issues/901
I can admit that I don't really know what I'm doing ATM :-)
#systemd
https://github.com/himmelblau-idm/himmelblau/issues/901
I can admit that I don't really know what I'm doing ATM :-)
#systemd
Jarkko Sakkinen
jarkko
Edited 5 months ago
@Foxboron @achilleas I have defacto answer for question four: https://www.joelonsoftware.com/2000/04/06/things-you-should-never-do-part-i/
Jarkko Sakkinen
jarkko
@Foxboron Full spam thread summarized: https://github.com/tpm2-software/tpm2-openssl/issues/120#issuecomment-3583885470
:-)
:-)
Jarkko Sakkinen
jarkkoJarkko Sakkinen
jarkko
@Foxboron OK that is great. Once there is a IETF draft I don't consider it as a Microsoft proprietary product :-)
As a disclaimer, it's not that I would necessarily want to comment on that. I rather adapt and perhaps workaround key spec in my implementation that proactively drive it because it is simply not my thing :-) This is what happend with parentPublic as cache internally handles it. However, as a maintainer I feel safer to accept change if a key type is driven by a real spec, which is not the case with TPMKey ASN.1 definition (YET).
As a disclaimer, it's not that I would necessarily want to comment on that. I rather adapt and perhaps workaround key spec in my implementation that proactively drive it because it is simply not my thing :-) This is what happend with parentPublic as cache internally handles it. However, as a maintainer I feel safer to accept change if a key type is driven by a real spec, which is not the case with TPMKey ASN.1 definition (YET).
Jarkko Sakkinen
jarkko
@Foxboron This would also give better visibility to other communities such as *BSD communities. Or who know perhaps e.g., Haiku would want TPM keys too some day? It really cannot be driven like this forever and it is responsible act from me to block any attempts to do so (further).
Jarkko Sakkinen
jarkko
@Foxboron
OK, tpm2@lists.linux.dev is fine but there is no documented contribution model for the spec :-) It is fine for PoC'ing but unacceptable lock-in for a mainline kernel patch when going beyond importing public and private blobs.
For me "acceptable" here would mean actually having at least a draft in the official IETF pipeline. That would decouple "proprietary control".
E.g., like David has done:
https://datatracker.ietf.org/doc/html/draft-woodhouse-cert-best-practice-00
IETF is not a single stakeholder properietary entity and there's a working model for reviewing and improving drafts.
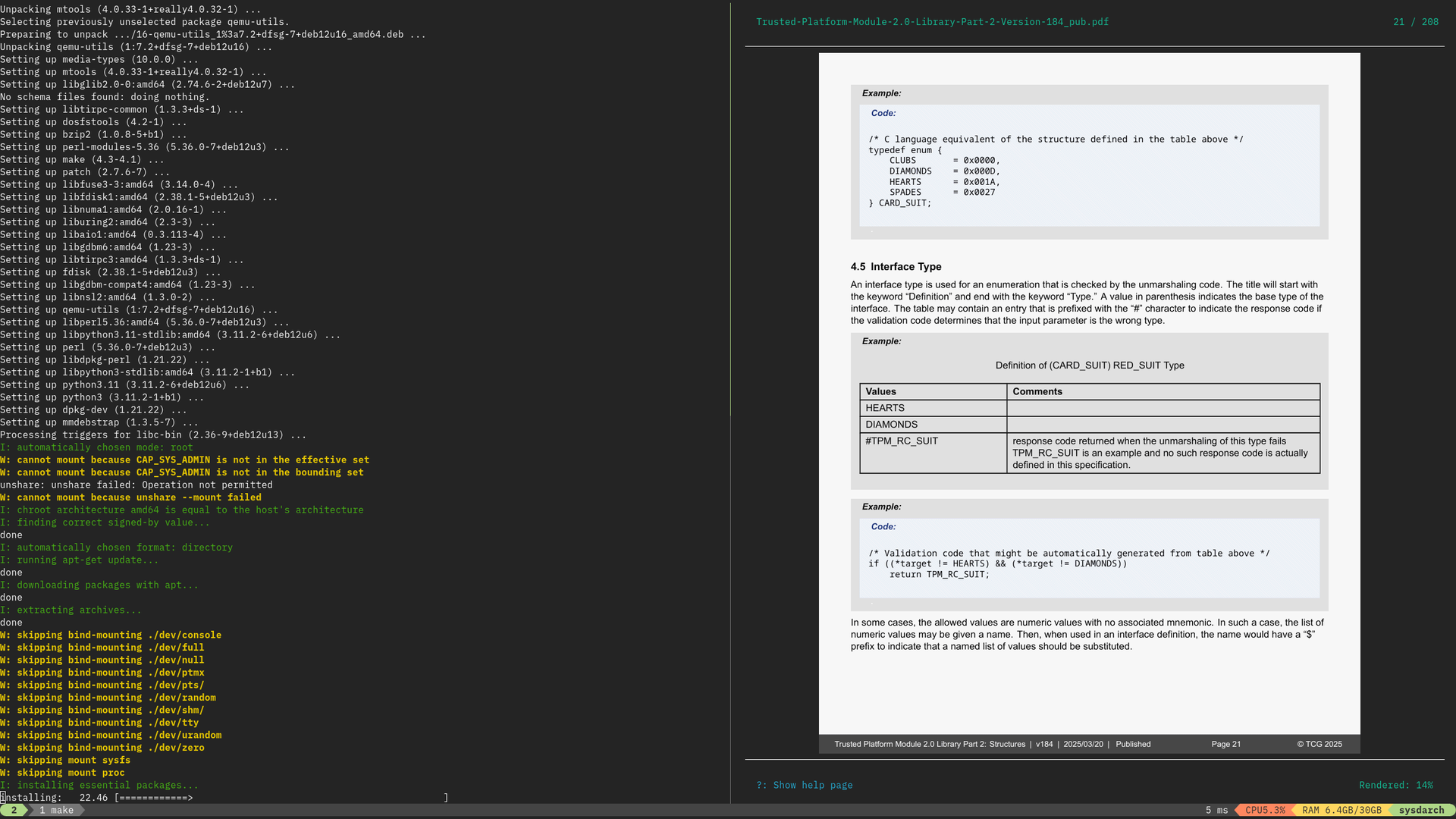
Backing story with my own Rust TPM2 stack is actually exactly this spec. I created a patch set [1] over a year ago to implement TPM2 parts of this spec but felt that I could not finish it with quality standards that would make me happy because lack of a proper tools for testing the patch set :-)
[1] https://lore.kernel.org/linux-integrity/20240528210823.28798-1-jarkko@kernel.org/
OK, tpm2@lists.linux.dev is fine but there is no documented contribution model for the spec :-) It is fine for PoC'ing but unacceptable lock-in for a mainline kernel patch when going beyond importing public and private blobs.
For me "acceptable" here would mean actually having at least a draft in the official IETF pipeline. That would decouple "proprietary control".
E.g., like David has done:
https://datatracker.ietf.org/doc/html/draft-woodhouse-cert-best-practice-00
IETF is not a single stakeholder properietary entity and there's a working model for reviewing and improving drafts.
Backing story with my own Rust TPM2 stack is actually exactly this spec. I created a patch set [1] over a year ago to implement TPM2 parts of this spec but felt that I could not finish it with quality standards that would make me happy because lack of a proper tools for testing the patch set :-)
[1] https://lore.kernel.org/linux-integrity/20240528210823.28798-1-jarkko@kernel.org/
Jarkko Sakkinen
 repeated
repeated
OpenAI says dead teen violated TOS when he used ChatGPT to plan suicide.
Ghouls gonna ghoul: Facing five lawsuits alleging wrongful deaths, OpenAI lobbed its first defense Tuesday, denying in a court filing that ChatGPT caused a teen's suicide and...
https://jwz.org/b/ykxy
Jarkko Sakkinen
jarkko
Edited 5 months ago
@Foxboron Personally I think we don't have at this point a working model for spec. It's essentially a proprietary spec because a single Microsoft employee controls it. For me that means that is solely Microsoft controlled spec which is not right.
Up until that is changed, I cannot e.g. accept patches that would add policies for trusted keys. Not saying it should be located in kernel tree but there should some kind of shared repository to discuss about it and propose updates.
In kernel we support only public and private fields essentially with parent auth value and that is what it stays up until there is "community edition" of the spec.
E.g., for me IMA it might be useful if one could apply policy sealed trusted key as the anchor of trust.
Up until that is changed, I cannot e.g. accept patches that would add policies for trusted keys. Not saying it should be located in kernel tree but there should some kind of shared repository to discuss about it and propose updates.
In kernel we support only public and private fields essentially with parent auth value and that is what it stays up until there is "community edition" of the spec.
E.g., for me IMA it might be useful if one could apply policy sealed trusted key as the anchor of trust.
Jarkko Sakkinen
jarkko
Edited 5 months ago
@Foxboron Now I exactly recall why it is less important now. I do the trick inside cache i.e. I have separate encoding for cache policies, which retain e.g. information about parent's public field. That way I get most of the convenience without having to break the file format. At the time I did not even know that I will have vTPM cache eventually :-) Things happened quite fast (and without much sleep)