Posts
5549Following
349Followers
548Jarkko Sakkinen
jarkkoJarkko Sakkinen
jarkkoJarkko Sakkinen
jarkkothe feature has nothing to do with hard real-time operating systems but some nice patterns used by #rtic have inspired me to find a right angle:
https://rtic.rs/2/book/en/
It's cool project IMHO and nice box of ideas how to do low-level and #embedded in rust.
#rtos
Jarkko Sakkinen
jarkkoI wonder what is the policy of putting something to scripts/ (not to vmlinux) that is written with #Rust? I.e. build time utility. Just curious.
And actually, since bindgen is installed from crates.io, not from kernel tree, should it be actually submitted there, and not to the kernel tree?
Kernel documentation gives pretty bad rationale for bindgen being in Cargo: “The bindings to the C side of the kernel are generated at build time using the bindgen tool. A particular version is required.” I’m sure there are good reasons to install it using cargo but why the documentation does not list those reasons, no matter how obvious they might be to some.
So I guess I put my build time tool to crates.io because at least first it is an experiment, and secondly bindgen is managed like this. But even this does not conclude the story fully. I have no idea in what license that out-of-tree pulled build-time utility is expected to be. It is not documented, or at least I cannot find it documented anywhere.
Jarkko Sakkinen
jarkkoOther thing that puzzles in #Ethereum and #Swarm is that why waste bandwidth and CPU cycles to #JSON when you could #ASN1 the transaction like:
Root ::= SEQUENCE {
from INTEGER
to INTEGER
value INTEGER
gas INTEGER
gasPrice INTEGER
nonce INTEGER
data OCTET STRING
chainId INTEGER
}
Pretty trivial scalability optimization IMHO. Maybe I submit another talk just to say that hey use ASN1.
Jarkko Sakkinen
jarkkoJarkko Sakkinen
jarkkoAlso, here the cool part considering is really the ASN.1 compiler, which could take advantage of procedural macros to spit out snippet of that bytecode. Because it is part of kbuild shenanigans it could be enabled potentially earlier than actual Rust features in vmlinux.
Doing this might also be a way to find better guidelines on how to use Rust in kernel.
#linux #kernel #Rust #rustlang
Jarkko Sakkinen
jarkkoThen gccrs would need to be on par only on that subset to be enabled for kernel build, which is first and foremost important thing for defconfig.
I implemented first versions of WebGL support back in 2010 for QtWebKit, which then spread to GtkWebKit and EFLWebKit. From that background I know how nicely that project copes with C++ and its crazy features :-)
Jon Greig
jgreig@ioc.exchangeNIST said it has awarded a new contract to an outside vendor that will help the federal government process software and hardware bugs added to the National Vulnerability Database (NVD).
NIST wouldnt say which vendor was hired
https://therecord.media/nist-nvd-backlog-clear-end-fiscal-2024
Jarkko Sakkinen
jarkkoLWN.net is now @LWN@lwn.net
LWN@fosstodon.orgA plea for more thoughtful comments https://lwn.net/Articles/975597/ #LWN
AndresFreundTec
AndresFreundTec@mastodon.socialHere are the slides for a talk I just gave about using perf c2c to find cache line contention in postgres:
https://anarazel.de/talks/2024-05-29-pgconf-dev-c2c/postgres-perf-c2c.pdf
Jarkko Sakkinen
jarkkoI think there would be still space for systems programming language with a constraint from day zero that it would 1:1 compatible with plain C”s binary layout and memory model:
- Roughly just
.text,.bss,.rodataand,data. - No symbol mangling at all.
All the memory safety etc. fancy features would be then designed within exactly those constraints.
#Rust is essentially a derivative of C++ when compiled to binary, which does not really make it a strong competitor for plain #C. It can substitute C in many cases for sure, just like C++ did, but there’s always need for minimal systems programming language, which also looks elegant in binary, not just in source code.
A compiled C program can be quite easily understood with a binary with no debug symbols at all if you understand the CPU architecture well enough. That is, and will be a strong asset for C.
Jarkko Sakkinen
jarkkoMy game plan for the next weekends Ethprague is this:
- Introduce roles in authentication: user and machine both I think should be represented with their own private keys. I.e. consider ENS as a fancy LDAP that the machine can access.
- Represent asymmetric TPM2 keys (
tpm2_key_rsa,tpm2_key_ecdsa) as a way to give a guarded identity for the machine (or node). - The lack of
TPM_ECC_P256_K1in TCG Algorithm Repository means that TPM’s cannot natively store Ethereum private keys. Could and should change tho. - Workaround that I’m going to do after my first patch set is completed: software ECDSA for p256k1, i.e. signing and verification. Allows to root the keychain to an asymmetric TPM2 key.
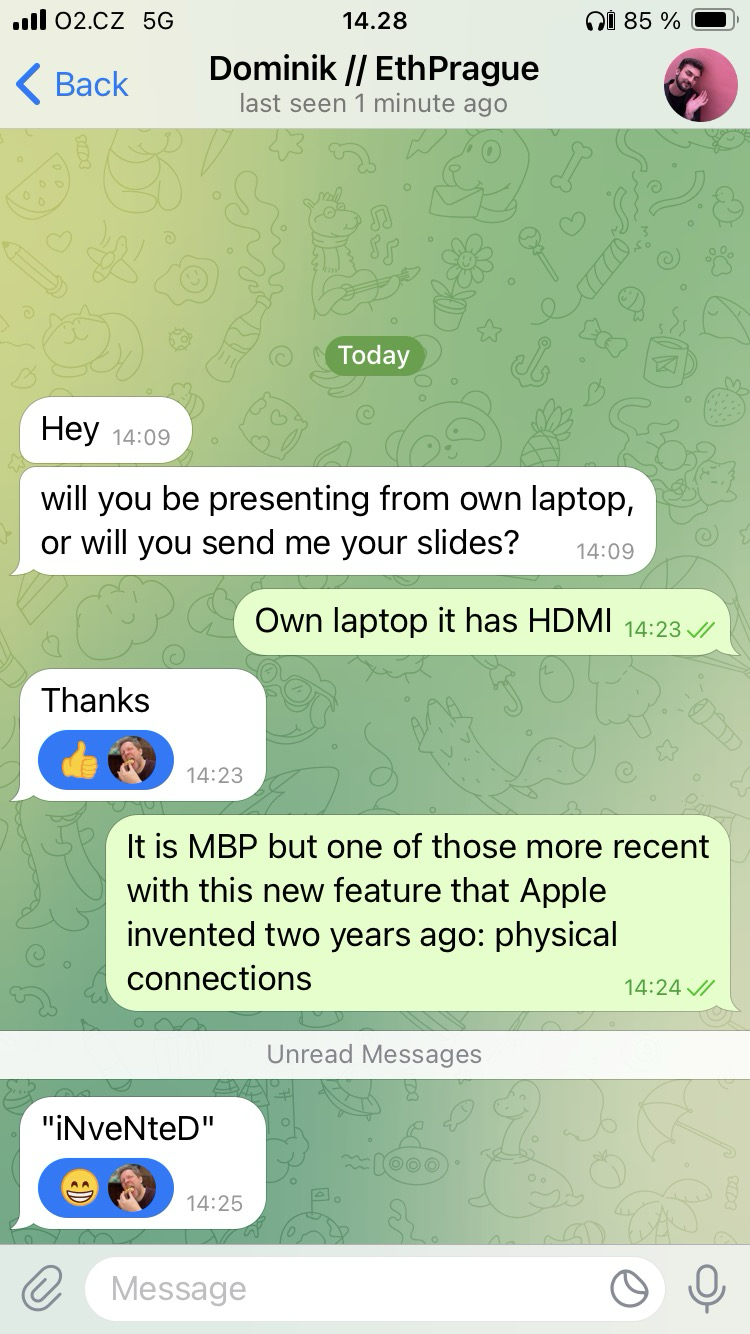
Feels like 25-30 mins to me. Most importantly, not much knowledge required of #Ethereum, which is pretty alien topic to me :-) About to head soon to the #Tampere airport.
I’m not really even a fan of blockchains or cryptocurrency but I still think that it is good to provide safe and usable mechanisms for any legit task that user wants to use Linux for. So thus I want to enable those and free of charge, in order to keep my position regarding this topic (no affiliations). I only benefit flights to Prague from this work (pay for Airbnb myself).
CONFIG.SYS: LOADHIGH
loadhigh@bitbang.socialI completely forgot I uploaded VistaPro 3.20 (the scenery renderer) to the Internet Archive, where you can run it from your browser. For those sudden urges of wanting to create some landscapes.
https://archive.org/details/vistapro320
Includes the MakePath tool.
Don't forget to take screenshots of your creations! Nothing can be retrieved from the disk the in-browser DOSBox keeps, as far as I know.
(Please be patient with the Archive's speed, they're dealing with persistent DDoS attacks at the moment)
Jarkko Sakkinen
jarkkoWhile developing asymmetric TPM2 keys, and reviewing TPM bus encryption earlier, I came to realize that both tpm2-tools and ibmtss feel unintuitive.
So I started to seek, if some had ever backed up my old tpm2-scripts, from which kselftest was inherited. I did not have anymore any repo for that one.
With Google I luckily found a backup from the Github profile of @colinianking, so thank you for that. Then I just copied over latest version of just tpm2.py (GPL/BSD dual-licensed file).
Probably will have some incompatibility issues with old scripts and updated main module (less than 10 updates in its total life-time tho) but I will fix them as soon as I need to test anything.
Anyway, a new and to-be-lean TPM2 hacking tool has been initiated: tpm2ctl (there’s no even file of that name yet but definitely will be at some point ;-)).